Understanding zkTLS in one article: Secure information transmission, the next new narrative of ZK?
Original article by: Decentralised.Co
Original translation: TechFlow
Blockchain Oracles: Blockchain APIs for Public Data
zkTLS: A blockchain API for any data
Zero-knowledge transport layer services (zkTLS) could be the death blow to closed corporate giant networks. Emerging networks now have the ability to compete with giants like Facebook and Amazon by leveraging zkTLS.
zkTLS allows users to permissionlessly migrate any of their identities on the internet, providing a powerful way for new networks to leverage existing ones. It enables users to switch freely between different platforms without having to start from scratch. Most importantly, it does this without compromising data privacy and security.
We are seeing crypto applications leveraging zkTLS in creative ways.
zkPass allows users to verify their traditional credit scores on-chain. OpacityNetwork allows Uber drivers to transfer their ratings to teleportxyz . It also enables drivers and restaurants to migrate their reviews from DoorDash to NoshDelivery .
Here’s how zkTLS works:
Transport Layer Security (TLS) secures more than 95% of Internet connections. It represents the “s” in “https” in most URLs. TLS connections ensure:
The interaction between a server (like your bank) and a client (like your phone) is trusted.
The data is confidential.
Strong data integrity.
zkTLS introduces a third-party verifier to verify the security of communications between the client and the server without compromising security. There are two main ways to achieve verification:
Proxy-based: A proxy server acts as an intermediary, monitoring encrypted communications and partially decrypting them to verify the client's credentials.
Multi-party computation (MPC) based: Clients and verifiers interact with the server, enabling the verifier to prove the authenticity of the message, while the server is unaware of the verifier's existence.
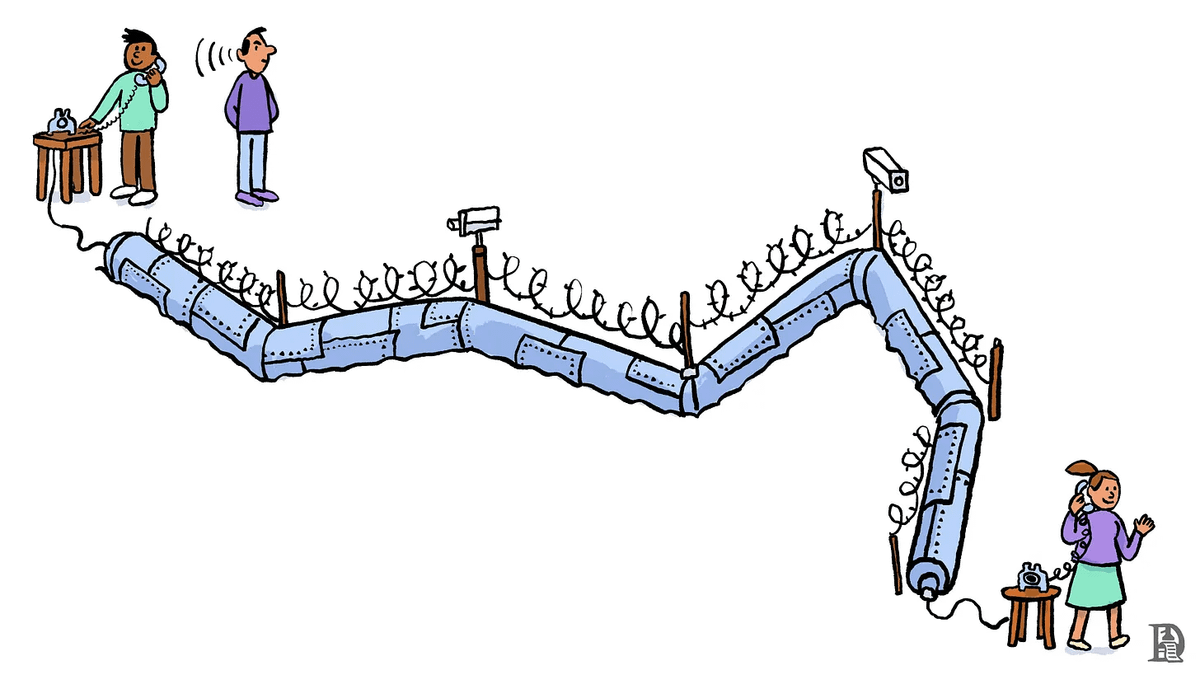
To maintain privacy, clients use zero-knowledge proofs to prove specific facts about the data without revealing the actual information.
For example, a proof could prove that their bank balance was over $1000 on a specific date, rather than the specific amount. Or, I could prove that my wallet belongs to a verified Indian citizen, without revealing other details like my name or date of birth.
These proofs can be recorded on the blockchain, where they exist permanently for other applications to access and verify.
Controlling users’ data holds power over internet giants, allowing them to create networks based on personalized experiences that lock users in. zkTLS breaks down the walls that trap billions of people today, creating a more open, decentralized future.



