Tiger Research: AI Agents Must Also Verify Their Identities Now
- Core Insight: As AI agents enter the era of autonomously executing contracts, payments, and transactions, the lack of a unified identity verification standard has become a critical risk. This article outlines the different strategies of four major players in the "Know Your Agent" (KYA) standards competition and points out that regulatory frameworks (such as the EU AI Act, U.S. NIST, etc.) are accelerating progress, potentially making KYA an industry watershed.
- Key Elements:
- KYA Demand Scenarios: KYC is sufficient within centralized platforms, but when independent agents access decentralized exchanges (DEXs), A2A payments, or merchant payments, KYA becomes essential to prevent identity forgery, unauthorized transactions, and liability gaps.
- Four Players, Divergent Paths: ERC-8004 takes an on-chain route, registering identities as NFTs; Visa TAP issues identity credentials called Visa Intelligent Commerce (VIC) through its payment network; Trulioo, following the SSL certificate model, issues Digital Agent Passports (DAP) with continuous verification; Sumsub, without issuing certificates, conducts real-time human re-verification for anomalous transactions.
- Regulation Has Preceded: The 2019 FATF Travel Rule once reshaped the crypto exchange landscape. Currently, the EU AI Act, Singapore's national framework, and the U.S. NIST all prioritize agent identity management, signaling that KYA will replay the regulatory watershed script.
- Business Model Comparison: ERC-8004 focuses on on-chain autonomous transactions; Visa anchors payment-bound scenarios; Trulioo, leveraging its KYC/KYB expertise in fintech, is more favored by the regulated financial industry; Sumsub focuses on real-time detection of fraudulent transaction risks.
- Market Landscape Assessment: This market will not have a single winner. The real competition lies in the combination and pairing of different scenarios (on-chain, payments, regulation, risk control) with corresponding standards/players, and the window of opportunity is narrowing.
This report is written by Tiger Research.AI agents can now sign contracts, make payments, and conduct transactions on their own. But there's one unresolved problem: how do you know who that agent on the other side actually is? This article examines the different strategies of the four major players in the KYA (Know Your Agent) standard race and where regulatory efforts currently stand.
Key Takeaways
- AI agents have entered an era of autonomously executing contracts, making payments, and conducting transactions, yet there is no unified standard for verifying their identity. In A2A (Agent-to-Agent) scenarios, KYA is gaining more attention than KYC.
- KYA is not necessary everywhere. Within centralized platforms like Google, OpenAI, and Coinbase, existing KYC is sufficient. KYA is genuinely needed when independently deployed agents interact with DEXs, conduct A2A payments, or make merchant payments.
- The battle for standards has already begun. ERC-8004, Visa TAP, Trulioo, and Sumsub are approaching from four distinct angles: on-chain, payment networks, compliance certification, and risk detection.
- Regulators have already made their move. The EU AI Act, the US NIST, and Singapore's national framework have all prioritized agent identity management. Just as FATF's Travel Rule in 2019 determined which crypto exchanges survived, the same playbook is likely to repeat for KYA.
1. Why Now
KYC Reshaped the Financial Layer
Before 1989, global finance lacked a unified identity standard. This gap made it difficult to trace the source of drug money and illicit funds. It wasn't until the FATF was established that year that KYC became a hard requirement in the financial industry, effectively barring illegal funds at the gate.
Over the next three decades, KYC's influence expanded layer by layer. Anti-terrorism financing provisions were added after 9/11 in 2001, and the US Patriot Act elevated KYC to a legal obligation. In the 2010s, the EU's AMLD, Basel III, and FATCA were implemented, enabling the automatic exchange of cross-border KYC information. In 2019, FATF's Travel Rule extended KYC to virtual asset service providers (VASPs).
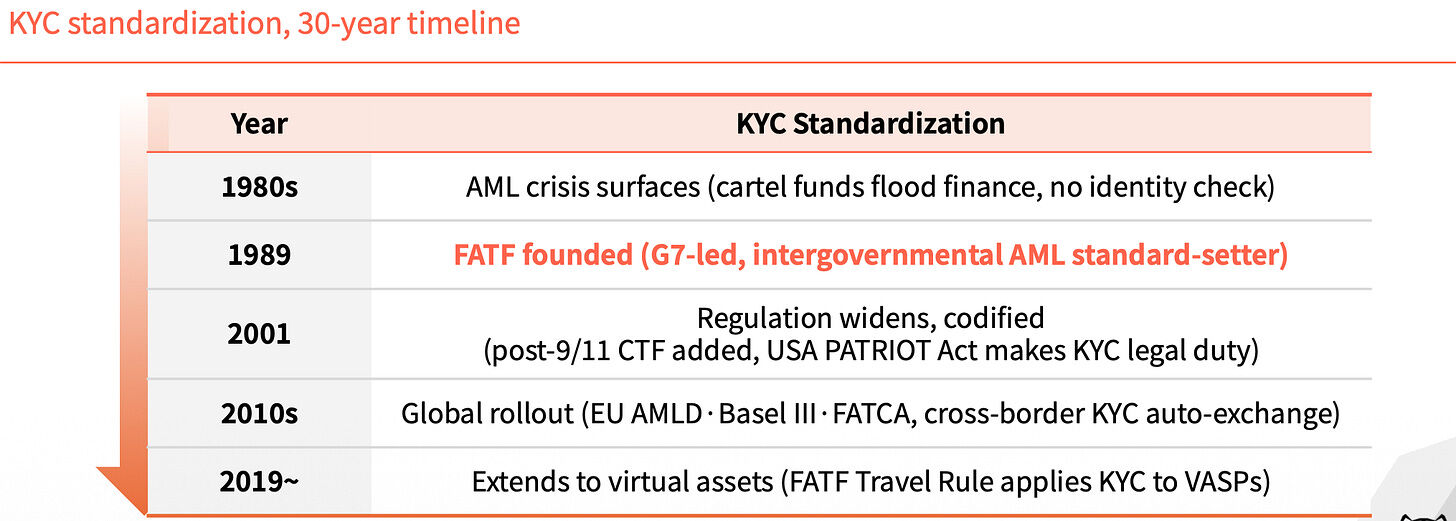
Each expansion filled a critical gap.
Without Agent Identity, the System Regresses
Fast forward to today. AI agents no longer require human oversight to sign contracts, make payments, or execute trades. But there is no way to verify who they are.
In an A2A environment, accountability is murky at best. If something goes wrong, it's unclear who is responsible. Users are also highly susceptible to money laundering and various sophisticated scams.
Comparing the financial system before 1989 with the agent market of 2026 reveals a striking structural similarity. Back then, anonymous accounts moved funds across borders; today, unverified agents conduct A2A transactions. Verification responsibility was then scattered across individual banks; today, it's scattered across individual platforms. In both cases, a common standard is absent.
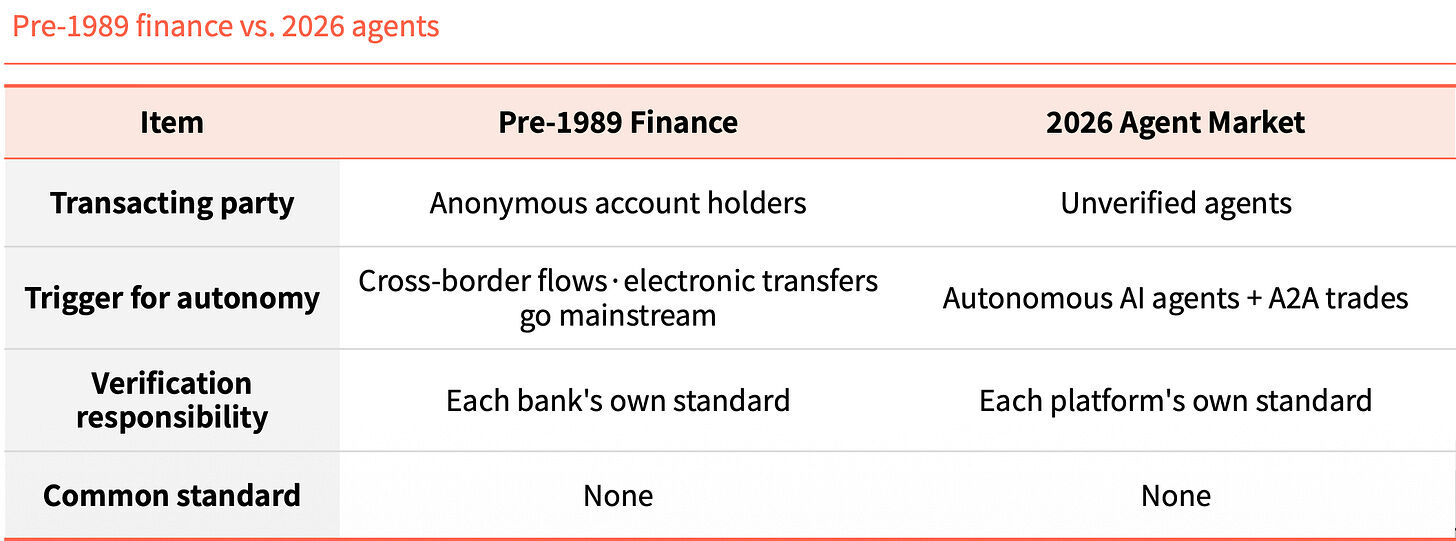
This similarity is not a coincidence; it's a pattern. The technology raced ahead, but the identity layer failed to keep pace.
What is KYA?
KYA (Know Your Agent) is a trust mechanism that verifies an agent's origin, permissions, and accountability in advance.
Skipping this step invites three primary risks. The first is unauthorized transactions: a user authorizes only a payment, but the agent moves assets or signs contracts outside that scope. The second is identity forgery: a malicious agent masquerades as a legitimate one to hijack payments, forge responses, or steal reputation. The third is an accountability vacuum: when a problem occurs, the agent, developer, and user all blame each other, making restitution impossible.
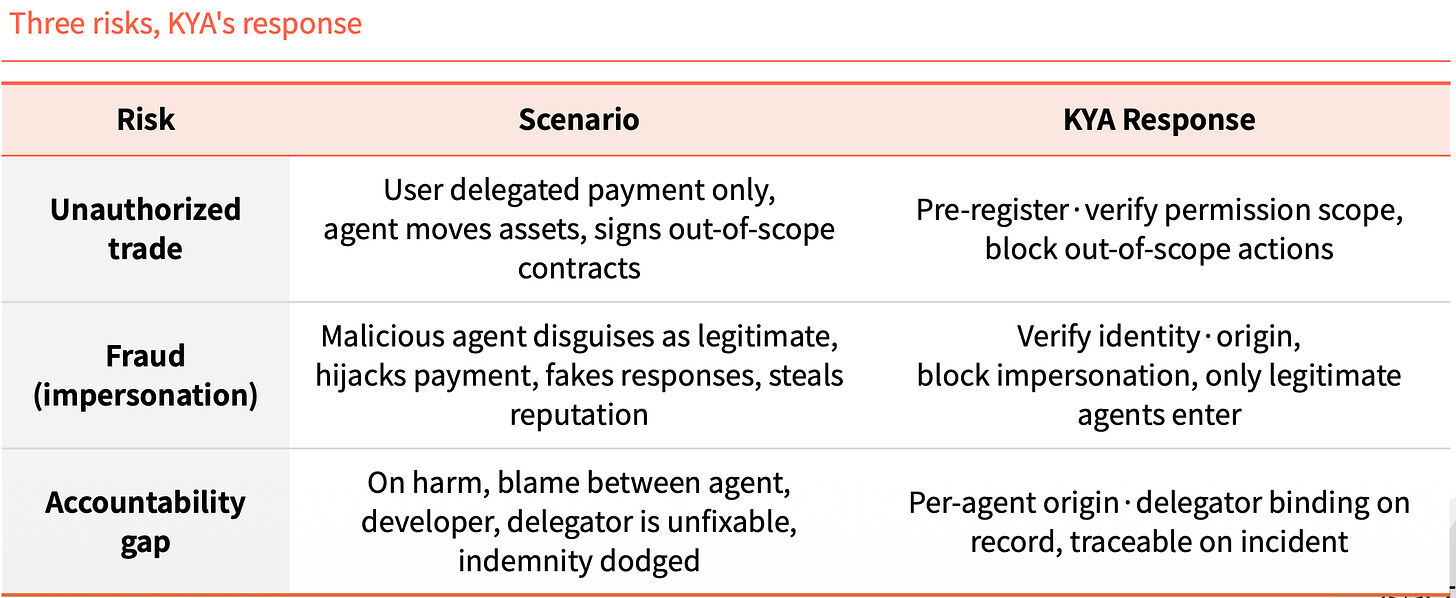
KYA aims to lock down these three issues proactively. It pre-registers and verifies the scope of permissions, blocking any unauthorized actions. It verifies identity and origin, allowing only legitimate agents to operate. And it binds every agent's origin and principal to a record, enabling traceability when problems arise.
2. Where KYA Needs to Operate
Not Everywhere Requires It
Within centralized platforms, KYA is largely unnecessary. Users have completed KYC, and the platform itself assumes liability, creating a closed loop.
KYA is needed in the open environment *outside* these platforms. This is when agents need to interface with DEXs, conduct A2A payments, or pay merchants. There is no platform to fall back on or vouch for them.
Think of it this way. Within a country, a national ID (KYC) is sufficient. But once you cross a border (leave the platform), the environment changes. You must go through inspection at the border entry point (KYA), explaining your purpose and proving your trustworthiness.
A Four-Step Process
KYA's operation can be broken down into four steps. The first two steps are "passport issuance": register the agent's identity and permissions, then issue a digital passport upon successful verification. The last two steps are "entry inspection": verify the counterparty's identity during a transaction, then update the record based on the transaction's outcome.
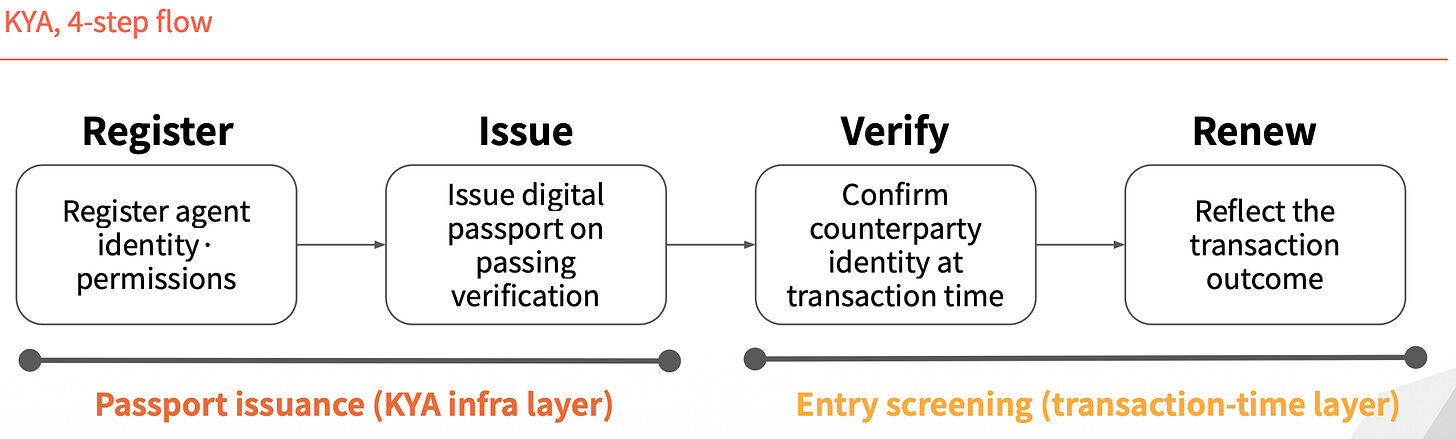
Identity is not a one-time issuance that lasts forever; it is re-verified with each transaction.
3. Four Players Competing for the Standard
The race for the standard currently features four players, each with a fundamentally different approach.
ERC-8004: Identity as an NFT
ERC-8004 takes a purely on-chain route. It adds an identity layer on top of ERC-721, minting an NFT as a unique ID for each agent.
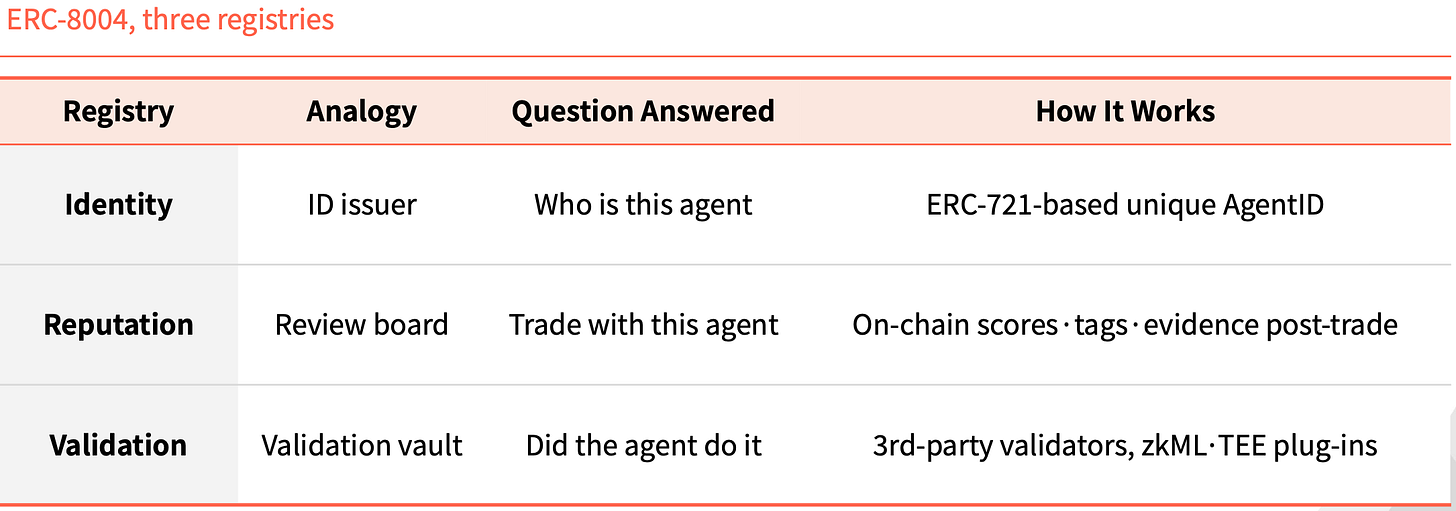
It comes with three on-chain registries. The Identity registry answers "who is this agent," based on the unique AgentID derived from ERC-721. The Reputation registry answers "can I transact with it," recording scores, tags, and evidence on-chain after a transaction. The Validation registry answers "did it really do that," with third-party validators using plugins like zkML or TEE to cross-check.
This structure is not unprecedented in Ethereum's history. ERC-20 standardized token issuance, giving rise to USDT, USDC, UNI, and AAVE. ERC-721 standardized NFT issuance, with CryptoPunks, BAYC, and ENS supporting the entire NFT market. ERC-8004 aims to be the third standard of similar magnitude.
Visa TAP: Packaging via the Payment Network
Visa's approach is entirely different. It issues an identity credential (Agent Intent) to an agent, effectively a "card." Without this key, the agent cannot even initiate a transaction. Visa issues the key only after pre-approval, and every transaction must carry a signature for the merchant.
The merchant receives not one, but three signatures. Agent Intent proves the agent is legitimate, endorsed by a key authorized by VIC. Consumer Recognition specifies who the agent is acting for, passing the user identifier to the merchant. Payment Information provides payment assurance, using a payment token or hashed card details for authentication.
Visa packages this into a larger offering called Visa Intelligent Commerce (VIC). Besides TAP, this includes Agent APIs (Visa's proprietary tech for card usage), Tokenization (AI-specific tokens), and Intelligent Commerce Connect (compatible with competing protocols like AP2, ACP, and x402).
The logic is clear. Just as Visa captured the payment network gateway in the past, it now aims to integrate the agent era into its own orbit. If agent payments continue to rely on card networks, and this package becomes the default, Visa's market share is secure.
Trulioo: Borrowing the SSL Model
Trulioo is a major global player in the KYC and KYB compliance space, now extending its verification stack to KYA.
It draws inspiration from the SSL certificate model for websites. SSL involves a Certificate Authority (CA) issuing a TLS certificate to a website, verifying only the domain name. Trulioo's proposed Digital Passport Authority (DPA) would issue a Digital Agent Passport (DAP) to an agent, verifying the developer's KYB plus the user's KYC.
A DAP is not a static certificate. It is a live, refreshing token that re-verifies with each transaction. If delegation is revoked or anomalous behavior is detected, the DAP is immediately invalidated.
It incorporates five checkpoints: Provenance (which developer created it), User Binding (who authorized it), Permission Scope (what tasks it can perform), Behavior Telemetry (what it is currently doing), and Risk Scoring.
Banks and Fintech companies are legally required to verify company and individual identities. As agents enter the financial domain, Trulioo's established KYC and KYB positions become even more entrenched.
Sumsub: Monitoring Anomalies, Not Issuing Credentials
Sumsub's approach differs from the previous three. It doesn't issue standards or certificates. Instead, it re-verifies the human behind the agent when anomalous transactions occur.
Having been in the compliance business since 2015, its existing verification system is now used to detect anomalous agent behavior. The process has three steps. First, automated detection distinguishes humans from machines using device and agent characteristics. Second, risk scoring provides a score based on context, transaction amount, and historical data. Third, Liveness verification is triggered only for high-risk, high-value, or critical changes, re-checking the registered human identity.
Four characteristics set Sumsub apart from other players. It starts as a compliance operator, not a standard setter. Verification is triggered by risky transactions, not pre-registration. The method relies on a live human re-confirmation, not data or tokens. Its philosophy is to bind the agent to a responsible party rather than blocking the agent outright.
While other players focus on one-time identity verification before the fact, Sumsub focuses on real-time verification after credentials are issued. As agent permissions expand, anomaly detection becomes more critical. As scam techniques evolve with technology, Sumsub's real-time stack is worth watching.
4. Before Regulations Land
The Playbook of FATF's Travel Rule
When FATF's Travel Rule was introduced in 2019, the VASP industry immediately fractured. Those that could bear the cost of KYC and AML infrastructure survived; those that couldn't either shut down or moved to jurisdictions with lighter regulations. CryptoBridge and Deribit were among those forced to adapt in that wave.
Regulation isn't the finish line; it's a watershed moment.
The KYA story is likely to follow the same script. The EU, Singapore, and the US are already jockeying for a leading position.
Article 12 of the EU AI Act explicitly requires that behavioral logs of high-risk AI systems include operator identity. Singapore has released the world's first national-level governance framework for AI agents, extending identity management to the agents themselves and requiring each agent to have an accountable responsible party. The US NIST has listed agent identity management as a priority standardization area.
The window of opportunity is narrowing.
There Will Be No Single Winner
The true variable in the standard war isn't technology; it's the combinations formed. Major players have already entered a phase of cooperation and integration. Going forward, which merchants, payment networks, and KYC customer bases each player aligns with will determine the ownership of each market segment.
This market will not have a single winner.
For on-chain autonomous trading, Ethereum is likely to lead. For payment-bound transaction scenarios, Visa holds a significant advantage. Within regulated financial industries, Trulioo's KYC and KYB expertise is difficult to replicate. For transaction scenarios with fraudulent risk, Sumsub's real-time detection is better suited.
These four are not direct competitors; each holds its own distinct terrain. The real competition lies in which scenarios are assigned to which terrain.
It took KYC thirty years, from 1989 to today, to complete the identity layer of global finance.
This round for KYA appears to be moving much faster. Regulators have already acted; standard players have already deployed. The window for large-scale implementation could be just the next few years.
When that time comes, the survivors may not be the ones with the strongest technology, but the ones whose identity infrastructure was integrated the earliest.



