Crypto Influencer Attacked, Loses $24 Million: Poisoning or Kidnapping?
- Core Viewpoint: As cryptocurrency wealth becomes transparent on-chain, physical coercion attacks ("wrench attacks") targeting holders are surging, exposing the vulnerability of personal security beyond the technical safety system. This compels the industry and individuals to adopt new protection strategies.
- Key Elements:
- Security firm CertiK's report shows a 75% surge in "wrench attack" incidents in 2025, with related losses exceeding $40.9 million. Europe has become the highest-risk region, with France leading the world in case numbers.
- Attackers screen targets through public on-chain data or social media. Typical targets include retail investors with public holdings, industry executives and their families, OTC traders, and other weak defensive links.
- The key to personal protection lies in asset separation (e.g., setting up "decoy wallets"), physically isolating mnemonic phrases from signing devices, and strictly avoiding flaunting assets or itineraries on public platforms.
- For institutions or large holders, employing structural tools like multi-signature schemes and timelock contracts can fundamentally increase the difficulty of coerced transfers from a single point.
- The surge in physical attacks has drawn regulatory attention. Countries like France have begun discussing specialized legislation, and law enforcement agencies are updating personal safety guidelines for digital asset holders.
Original Author: ChandlerZ, Foresight News
"I have bruises on my body, I tried to resist, but my hands and feet are injured, I was cut with an axe, and there's nothing I can do."
On March 5, 2026, crypto influencer sillytuna posted an extremely brief tweet, claiming she had just been violently attacked, losing approximately $24 million worth of AUSD stablecoins. She described the case involving violence, weapons, kidnapping, and threats of rape. The police are now involved.
Sillytuna was the former holder of Punk #7523 (commonly known as the 'Covid Alien'), an NFT that sold for $11.7 million at Sotheby's in 2021, once setting a record for a single Punk auction.
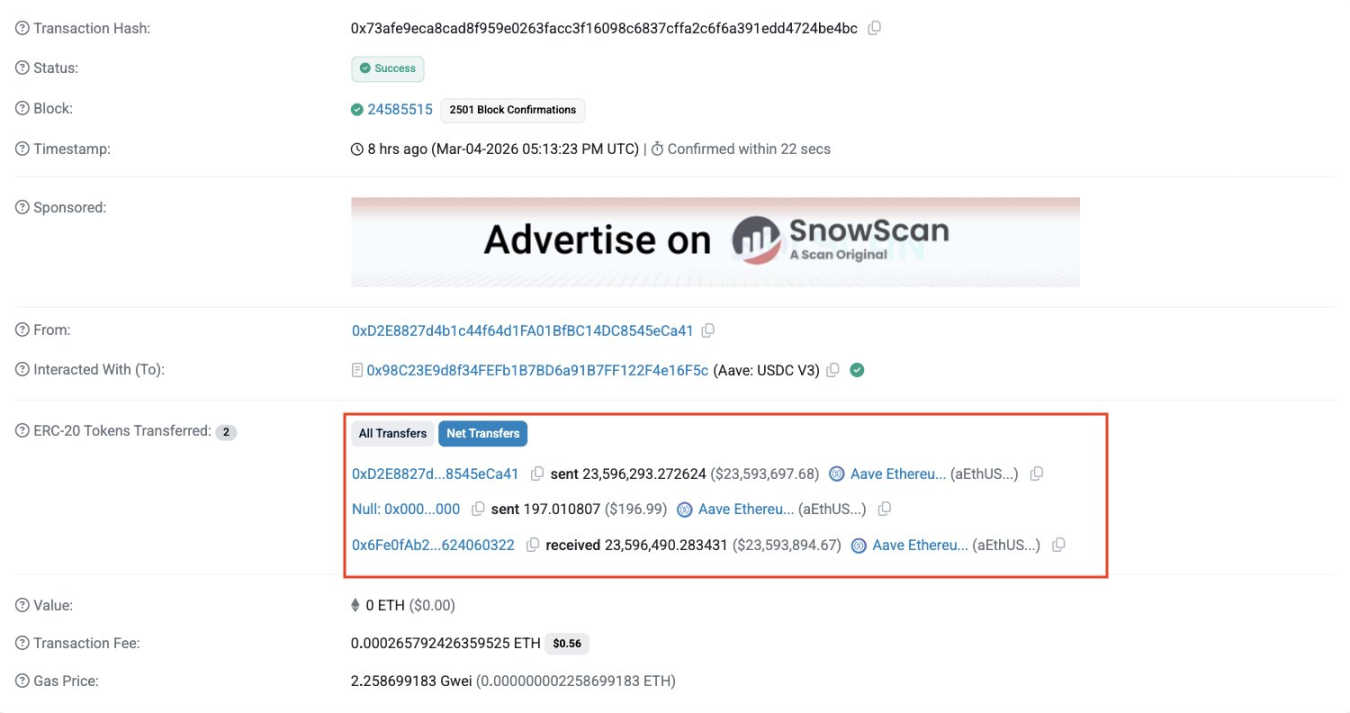
This tweet quickly spread within the crypto community. Security firm PeckShield monitored related on-chain transfers and preliminarily labeled it a 'Poisoning Attack,' a method that deceives users into transferring funds by using fake, similar-looking addresses.
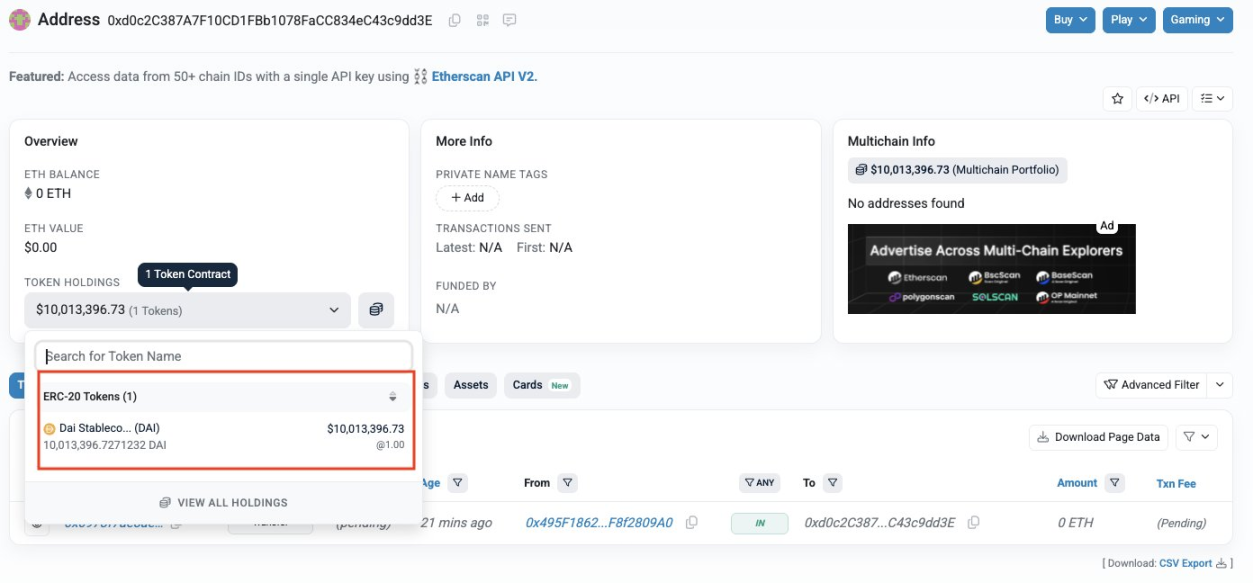
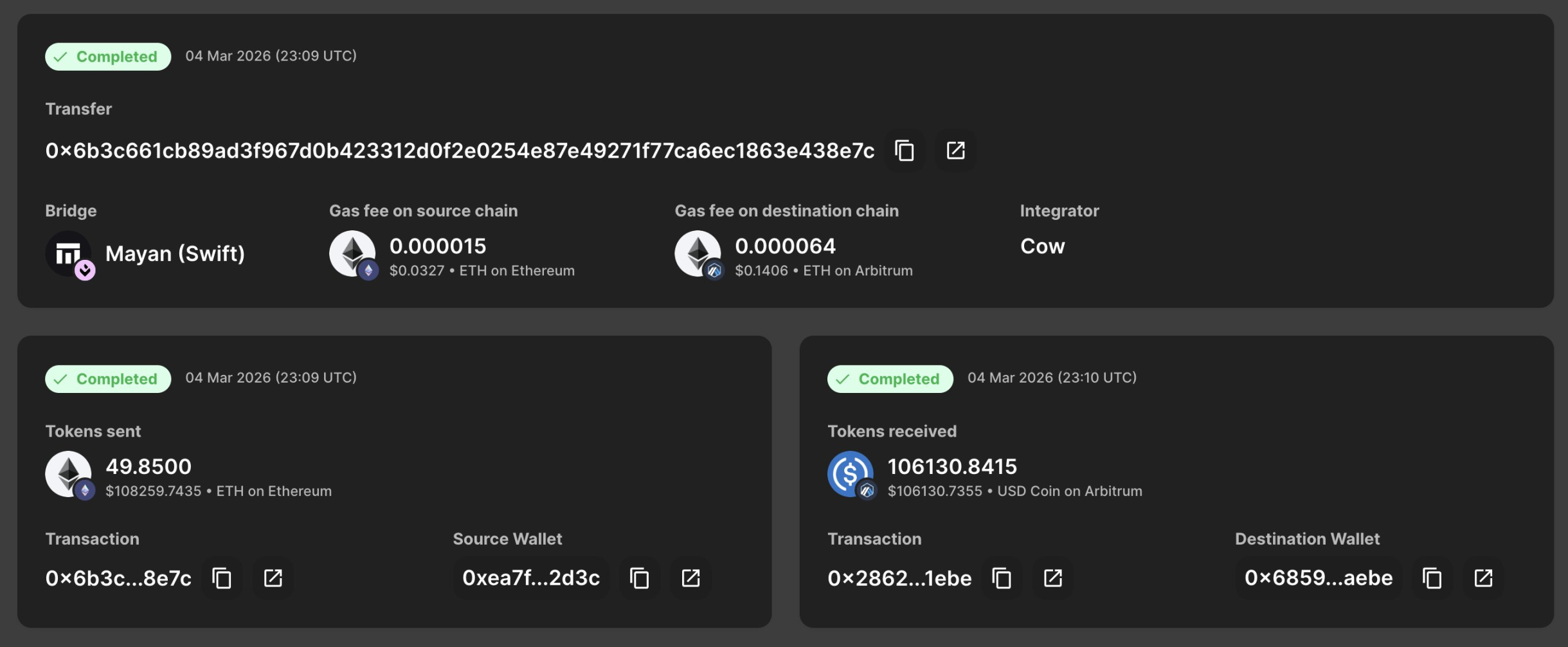
According to PeckShield monitoring, approximately 20 million DAI are currently held in two wallets controlled by the attacker (not yet mixed): the address starting with 0xdCA9 (about $10 million) and the address starting with 0xd0c2 (about $10 million). The attacker has already begun bridging small amounts of funds to Arbitrum.
There is a clear contradiction between the two narratives. If it were a poisoning attack, the victim was tricked into initiating the transfer, making physical violence an unnecessary prerequisite. If it were physical coercion, the attacker already possessed the victim's real identity and address.
Currently, the details of the incident await confirmation from police investigation, and some in the community have raised questions about whether it's a 'clout-chasing post.' Regardless of the final conclusion of this case, the panic it has triggered illustrates one thing:
In today's world of highly transparent crypto wealth, a single mistake in on-chain exposure can lead to a very real axe.
Not an Isolated Case: Physical Attacks Surged 169% in 2025
So-called 'wrench attacks' refer to attackers using physical means such as violence, intimidation, or kidnapping to force victims to surrender private keys or passwords. These attacks do not rely on technical vulnerabilities but directly target the individuals behind the crypto assets.
A report released by CertiK shows that 'wrench attacks' surged by 75% in 2025, with physical violence becoming a significant threat in the crypto space.
In terms of attack patterns, the report notes that kidnapping remains the primary method, with 25 incidents recorded for the year; direct physical assault incidents increased by 250% year-over-year, becoming one of the most concerning changes. Geographically, Europe became the highest-risk region globally for the first time. In 2025, Europe accounted for over 40% of known global incidents, with France recording the highest number of attacks worldwide, surpassing the US. Financially, confirmed losses related to wrench attacks in 2025 exceeded $40.9 million, a 44% increase year-over-year.
Jameson Lopp, Chief Security Officer at Bitcoin security company Casa and a long-term tracker of physical attack incidents, maintains a database covering over 225 verified cases to date. In 2025, this list grew at an unprecedented rate, and this data is also rapidly increasing in 2026.

Furthermore, as many victims choose silence due to fear, privacy concerns, or distrust of law enforcement, the actual number is likely much higher. The victim pool has expanded far beyond crypto elites, encompassing teachers, construction workers, firefighters, and their family members.
Three Landmark Cases in 2025
Case 1: Ledger Co-founder Kidnapped, Finger Severed (France, January 2025)
In January 2025, Ledger co-founder David Balland and his wife were kidnapped from their home in Vierzon, central France, and held separately. The attackers then sent a video of Balland's severed finger to another Ledger co-founder, Eric Larchevêque, demanding a ransom equivalent to 10 million euros in cryptocurrency.
After intervention by France's elite police unit GIGN (National Gendarmerie Intervention Group), Balland was successfully located and rescued. His wife was found hours later in a van. Most of the ransom that had been paid was tracked, frozen, and seized. Ten suspects aged between 20 and 40 were arrested. Prosecutors stated that if convicted, those involved could face life imprisonment.
Case 2: Paymium CEO's Daughter Attacked on Paris Street (France, May 2025)
On the morning of May 13, 2025, the daughter of French crypto exchange Paymium CEO Pierre Noizat was walking with her young grandson on a street in Paris's 11th arrondissement when three masked men intercepted her and attempted to force her into a van.
The attack occurred in broad daylight on a busy street and was captured on surveillance cameras. Noizat's daughter fought back fiercely, grabbing one of the guns and throwing it to the ground; passersby immediately joined in, with one picking up the gun and pointing it at the assailants, and another using a fire extinguisher to disperse them. The three assailants ultimately fled in panic.
Following the incident, French authorities launched an investigation centered on this attempted kidnapping, leading to charges against 25 individuals, including 6 minors. This detail sparked extensive discussion in French media about the 'Mexicanization of France.'
Case 3: Former US Police Officer Carries Out Crypto Wrench Attack (Los Angeles, 2024-2025)
In late 2024, a former Los Angeles Police Department (LAPD) officer was convicted by a jury for physically coercing crypto holders and forcing victims to transfer approximately $350,000 worth of Bitcoin. The case's uniqueness lies in the perpetrator's law enforcement background—meaning he possessed professional knowledge on how to evade surveillance and apply coercion.
The verdict has been widely cited in the crypto community because it shatters the assumption that physical attacks only come from street criminals.
Why Are Crypto Holders Particularly Vulnerable, and What Can Users Do?
The core assessment of the CertiK report is that attackers are actively selecting targets based on risk-reward analysis, prioritizing the combination of 'high potential reward and low security defense.' This logic gives rise to four typical target categories.
The most direct are retail investors who publicly display their asset holdings on social media; their on-chain balances are viewable, and their security is almost zero. Industry executives and protocol founders represent higher value; although they often have security measures, they remain exposed during travel or public events. The third category, family members and close friends, is often overlooked. Criminals know that when a spouse, child, or elderly parent is controlled, the primary target will bypass any security protocols. Moreover, many family members typically lack basic operational security training, with protection levels far below that of the primary target. The fourth category is over-the-counter (OTC) traders. Attackers disguise offline transactions as normal business meetings, initiating a hijacking as soon as the victim provides proof of assets.
Simultaneously, attack surveillance methods have evolved from physical stalking to OSINT-driven digital footprint analysis. Attackers lock onto a target's vulnerable time windows weeks before acting. For the entry stage, impersonating delivery personnel or utility workers remains the most effective infiltration method, catching victims psychologically unprepared. Once inside, they deploy Faraday bags and signal jammers to cut off device network connections and forcibly separate victims from family members.
The era of relying solely on seed phrases is over. The human remains the weakest single point of failure in the entire security system.
At the individual level, the most crucial step is establishing a separated architecture of 'decoy wallet + core wallet.' The decoy wallet needs to hold a seemingly reasonable small amount of assets. An amount too small could anger the attacker, triggering further violence. Under coercion, it provides an outlet for compromise, protecting the core assets from being accessed. Meanwhile, seed phrases and signing devices must never be stored in the same location. The ideal method is to deposit seed phrases in a bank safe deposit box rather than keeping them at home.
In daily behavior, 'do not flaunt' is the baseline. Avoid posting wallet addresses, asset screenshots, or travel itineraries on any public platform. Use a dedicated phone for travel, maintaining only minimal account permissions. Do not install high-value wallet applications on devices carried daily. Conduct high-value transactions only on dedicated, non-portable computers.
For individuals and institutions holding large assets, the report suggests two structural tools: Multi-signature schemes (e.g., 2/3 or 3/5) fundamentally eliminate the possibility of a single person being coerced to transfer funds; Time-lock contracts impose mandatory delays on withdrawals exceeding a set threshold, creating a window for external intervention.
Beyond this, CertiK lists three categories of warning signs worth noting: receiving unsolicited two-factor authentication codes (may indicate attackers have obtained your digital credentials and are testing responses); real-world anomalies, such as unexpected deliveries you didn't order, or repeated harassment to confirm if a residence is occupied; and sudden contact from long-unheard acquaintances emphasizing the need for an in-person meeting. These three signal categories repeatedly appear in the case database but were rarely recognized as dangerous by the victims at the time.
This Is Not Just a Personal Security Issue
Every time Bitcoin hits a new all-time high, Jameson Lopp's database receives a batch of new entries. This correlation line between price and violence has been tracked by him for nearly a decade.
The crypto industry has spent fifteen years solving private key security issues, building wallets, protocols, and multi-signature architectures increasingly difficult for hackers to breach. But when attackers turn to the human body, these technological defenses become almost useless.
The sillytuna case remains controversial, but the question it raises is real: While the transparency of crypto wealth is a selling point for the industry, is it also drawing a hunting map for some?
France has begun discussing whether a specialized legal framework is needed to address crypto-related extortion crimes. Law enforcement agencies in regions like the UK and Singapore are also updating personal safety guidance for digital asset holders.
The next person confronted with an axe at their door may not be a billionaire. It could just be an ordinary user whose on-chain balance was seen by someone.



