下一代加密安全,不依賴設備,而是取決於隔離架構
- 核心觀點:下一代加密資產安全正從依賴硬體錢包等單一設備,轉向基於系統隔離、架構設計和後量子密碼學的「無硬體安全模型」,以應對複雜攻擊和未來風險。
- 關鍵要素:
- 硬體錢包的安全性建立在信任設備製造商、韌體及供應鏈的基礎上,這與加密行業去信任化的理念存在固有矛盾。
- 硬體錢包在交易簽名時需與聯網設備互動,攻擊者可利用惡意合約、假網站等手段篡改交易資訊,這是其關鍵現實局限。
- 隔離加密錢包透過分離私鑰管理、交易簽名和網路廣播環境,使攻擊者即使入侵聯網部分也無法直接獲取私鑰,實現了「架構即安全」。
- NIST於2024年發布首批後量子密碼標準,提示量子計算對現有加密演算法的破解風險已進入現實討論階段,需提前防範「現在收集,未來解密」。
- Lock.com等項目探索的無硬體安全模型,致力於透過開源、可審計的系統設計減少對單一物理設備或廠商的依賴,作為下一代安全基礎設施的早期方向。
In the past decade, hardware wallets have been a cornerstone of crypto asset security. However, as on-chain transactions become more frequent and attack methods grow more sophisticated, the limitations of this approach are beginning to surface. Security concerns now extend beyond whether private keys are stored offline to include transaction signing, online interactions, supply chain trust, and the long-term risks posed by future quantum computing. The next generation of crypto security is shifting from "relying on a more secure device" to "relying on a more reliable system architecture."
1. Hardware Wallets: Once the Most Trusted Security Solution
In the realm of crypto asset self-custody, hardware wallets have long been considered the most secure option. The concept of cold storage, championed by brands like Ledger and Trezor, has become a consensus among many crypto users: Private keys are stored on an offline device, transactions require physical confirmation, making it difficult for hackers to directly access user assets via the network.
For a long time, this logic held true. An offline device could indeed thwart most remote attacks. For early crypto users, hardware wallets provided a simple, clear, and tangible sense of security.
However, as the scale of crypto assets has grown and on-chain transactions have become more frequent, attack methods have also become more complex. A critical question has emerged: Are hardware wallets still secure enough? Are they merely the current mainstream solution, or the ultimate form of crypto security?
Against this backdrop, a growing number of security researchers are focusing on a new direction: isolated crypto wallets, which protect private keys and transaction signing through clearer system-level isolation.
2. Re-evaluating Hardware Wallets: Security Still Comes with a Trust Cost
Hardware wallets may appear secure, but their safety is built upon numerous prerequisites.
First, users must trust the device manufacturer. For instance, is the device firmware sufficiently secure? Has the supply chain been tampered with? Has the secure chip undergone reliable audits? These questions are nearly impossible for average users to verify independently.
Second, firmware updates can also introduce risks. Hardware wallets require regular system updates to patch vulnerabilities and support new features, but users have difficulty determining if an update is entirely trustworthy. In many cases, users simply have to trust the vendor.
Additionally, the physical device itself carries inherent risks. The device could be lost, stolen, seized, or even subjected to targeted physical attacks. Even if the device remains uncompromised, the recovery seed phrase used to restore the wallet can become a new point of vulnerability.
Therefore, the issue with hardware wallets isn't that they are "unsafe," but that their security still depends on the device, the manufacturer, and the supply chain. For an industry that emphasizes decentralization and minimizing trust, this dependency is being re-evaluated.
3. The Practical Challenge of Hardware Wallets: Always Interacting with Connected Devices
The core security promise of a hardware wallet is that private keys never leave the device. However, in real-world use, transactions must eventually be broadcast to the blockchain network.
This means that when signing transactions, hardware wallets typically need to interact with a phone, computer, or other internet-connected device. Whether via USB, Bluetooth, or QR codes, this interaction creates a potential point of risk.
Many attacks don't require directly stealing the private key. Attackers might tamper with transaction information, making users think they are signing a legitimate transaction while actually authorizing a malicious operation. They could also exploit malicious contracts, fake websites, clipboard hijacking, and other methods to trick users into completing dangerous actions unknowingly.
This highlights a practical limitation of hardware wallets: The device itself can be offline, but the user's transaction process can rarely be completely offline.
For users seeking enhanced security, stricter air-gapped devices exist, which are completely offline and transmit data only via QR codes. However, these methods are more complex to operate and difficult for average users to maintain consistently. Ultimately, most people end up making trade-offs between security and convenience.
Consequently, the industry is beginning to consider another possibility: Rather than relying on users to always operate their devices correctly, why not design a system that more clearly separates the private key, signing, and network connection components?
4. Isolated Crypto Wallets: Incorporating Risk Isolation into System Design
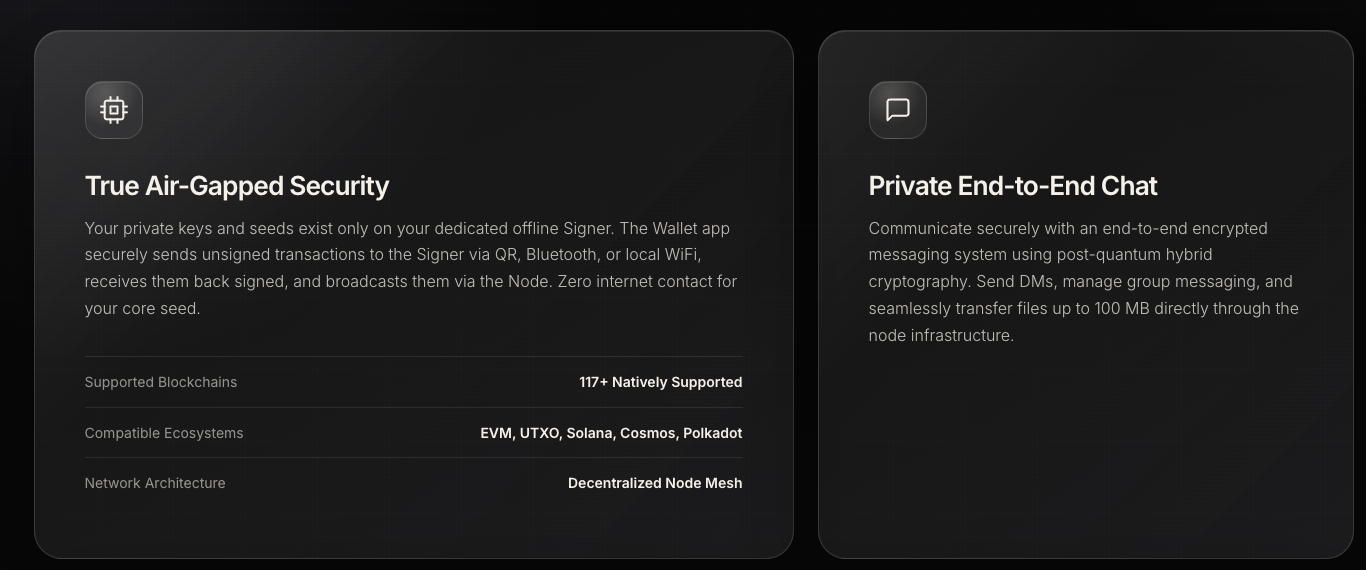
The core idea behind isolated crypto wallets is straightforward: Keep private key management, transaction signing, and network broadcasting in separate environments.
In simple terms, the private key and signing environment should remain as offline as possible, with no direct internet access. The connected part is only responsible for sending the already-signed transaction to the blockchain, without ever touching the private key.
The advantage of this design is that even if the connected part is compromised, the attacker can only access the signed transaction data, not the private key itself. For users, this means placing the most important asset key in a more secluded and less accessible environment.
The difference from traditional hardware wallets is that the latter rely more on a specific device for isolation, while isolated crypto wallets emphasize the structural design of the entire system. Security isn't solely dependent on a particular hardware device but on whether the key, signature, and network are genuinely separated.
This embodies the principle of "architecture is security": Security isn't just about buying a secure device; it's about proactively isolating dangerous pathways from the start.
5. Post-Quantum Security: Future Risks Are Entering Real-World Discussions
Beyond current attack risks, another issue gaining industry attention is quantum computing.
Many of today's cryptographic systems rely on algorithms like elliptic curve cryptography and RSA, which are still considered secure in traditional computing environments. However, if future quantum computers achieve sufficient power, these algorithms could face the risk of being broken.
While this may sound like a distant future problem, the global cryptography community has already begun preparations. The U.S. National Institute of Standards and Technology (NIST) released the first set of post-quantum cryptography standards in 2024, signaling that post-quantum security has moved from theoretical discussion to practical application preparation.
This issue is particularly critical for crypto assets because once blockchain assets are exposed to risk, the impact can be long-lasting. More notably, there is an attack strategy known as "harvest now, decrypt later," where attackers collect data today and attempt to decrypt it once quantum computing capabilities mature.
Therefore, post-quantum security isn't something to consider only after quantum computers become a reality. For users and projects holding assets long-term, early preparation is an integral part of any security strategy.
6. Hardware-Free Security Models: Reducing Reliance on a Single Device
Behind the isolated architecture lies a new security philosophy.
The traditional hardware wallet approach uses a physical device to mitigate risk. It stores private keys on the device, making it harder for attackers to access them over the network. This method is effective and has been validated by the market.
However, hardware-free security models attempt to further reduce dependence on specific physical devices. The key question they address is: Can we design a system where certain attack paths are inherently difficult to execute?
This approach brings several changes.
First, users no longer need to rely entirely on a single hardware manufacturer. Second, security is no longer completely tied to a specific chip or device. Third, if the system itself can be open-sourced and subject to community audits, security judgments can become more transparent.
This is not to say hardware wallets have no value. Physical devices can still be important tools within a security system. However, in next-generation crypto security infrastructure, they may no longer be the sole core component but rather one part of the overall security architecture.
7. Lock.com: An Early Explorer in This Direction
In this space, Lock.com is one of the earlier projects to explicitly explore isolated signing architectures and post-quantum security.
Lock.com is still in its early access phase and has not been fully publicly launched. It attempts to integrate private key management, offline signing, and post-quantum cryptographic concepts into a single hardware-free architecture, aiming to reduce the reliance of traditional hardware wallets on physical devices and vendor trust.
As the project is still in its early stages, many technical details and product features require further refinement. However, directionally, it represents a new way of thinking emerging in the industry: In the future, wallet security may no longer be solely about whether a device is secure enough, but also about whether the system architecture is clear enough and the isolation is thorough enough.
8. Crypto Infrastructure Is Moving from Point Solutions to Complete Systems
The emergence of hardware-free wallets is not an isolated phenomenon. It reflects a broader trend of upgrading the entire crypto infrastructure.
In the past, wallets, communication, storage, and transaction execution were often scattered across different products. Users had to combine various tools themselves and bear many operational risks. In the future, these functions may be integrated into more complete infrastructure.
Simultaneously, user perceptions of security are changing. Previously, many relied on brand reputation and device reviews. Now, more users and developers are focusing on whether the code is open source, the system is auditable, and the architecture is transparent.
In other words, the feeling of security is shifting from "I trust this brand" to "I can understand and verify this system."
In this trend, the direction represented by Lock.com offers a vision for next-generation security infrastructure: Security does not adhere to a single device or vendor but is embedded within the system architecture itself.
9. The Industry Is Asking a Different Question
A significant shift is occurring in the field of crypto security.
In the past, the most common question users asked was: Which hardware wallet should I buy?
Now, more and more people are starting to ask: Which security architecture should I trust?
This change in question indicates a deepening understanding of security within the industry. Hardware wallets have indeed protected vast amounts of user assets over the past decade, and their historical value is undeniable. However, as attack methods evolve, the risk of quantum computing enters the conversation, and new isolated architectures emerge, it is no longer certain that hardware devices are the final answer.
The next generation of crypto security infrastructure may reduce reliance on single physical devices, relying more on system design, key isolation, and forward-looking cryptographic solutions.
This transformation has already begun.



