On-chain Investigator ZachXBT Confirms: Axiom Employees Exploited Internal Privileges for Insider Trading
- Core Viewpoint: On-chain investigator ZachXBT released an investigative report accusing multiple employees of the crypto trading platform Axiom of long-term abuse of internal system privileges, illegally querying users' private wallet information and allegedly engaging in insider trading, exposing significant vulnerabilities in the platform's internal privilege controls.
- Key Elements:
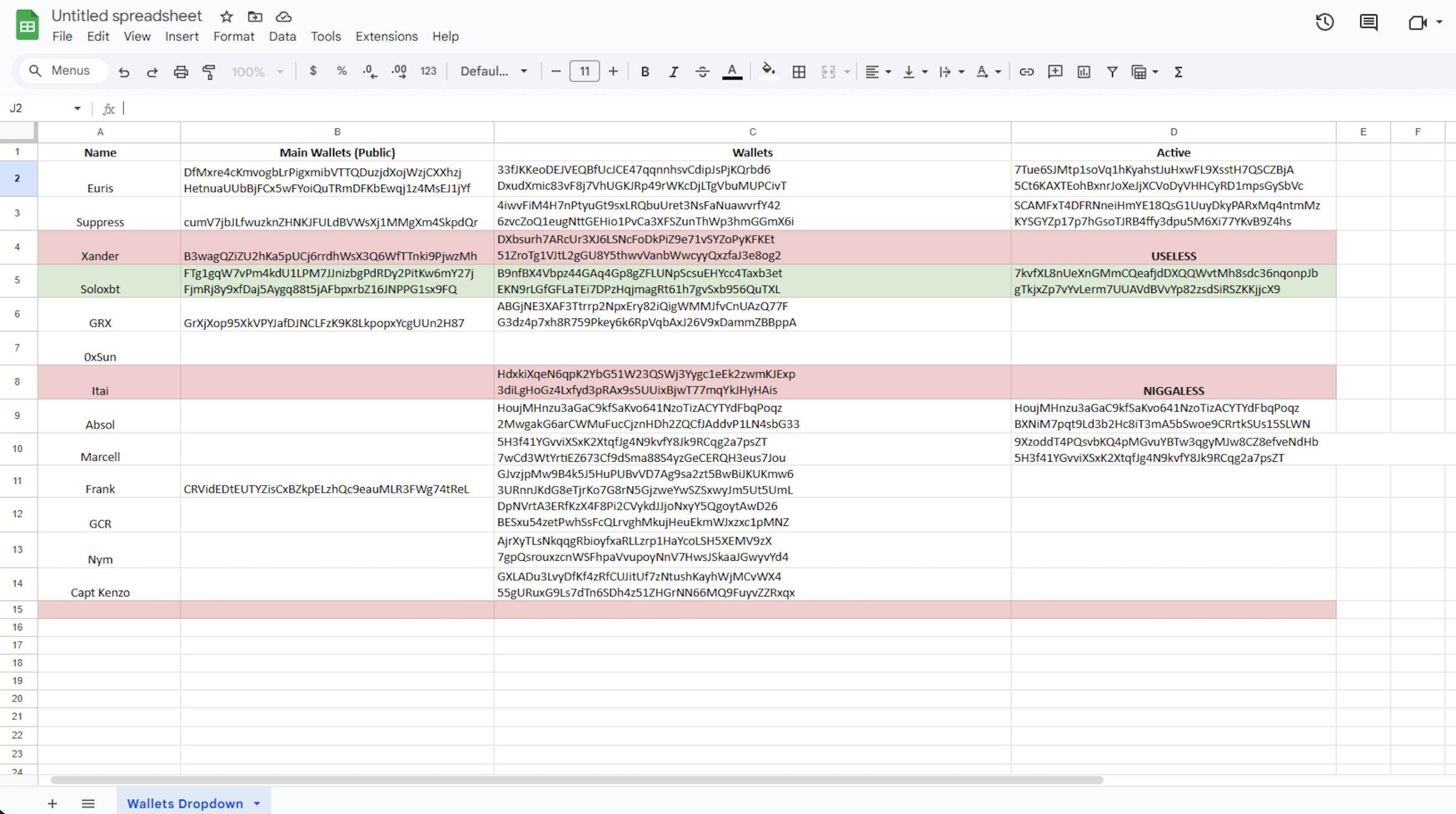
- Since early 2025, the involved senior employee, Broox Bauer, used backend privileges to track user wallets and established team query rules, with related actions evidenced by audio recordings and internal screenshots.
- Investigation evidence includes a leaked Google Sheets document summarizing KOL wallet addresses obtained through the internal backend, with multiple KOLs independently confirming their accuracy.
- In a February 2026 call, Broox detailed a plan to use privileges to help accomplices quickly profit $200,000; screenshots of his personal exchange account show the scheme had already generated returns.
- The report points out that Axiom's backend privilege settings are overly broad, allowing employees to view sensitive user information such as complete wallet lists and transaction history, and that the company lacks effective monitoring and privilege control mechanisms.
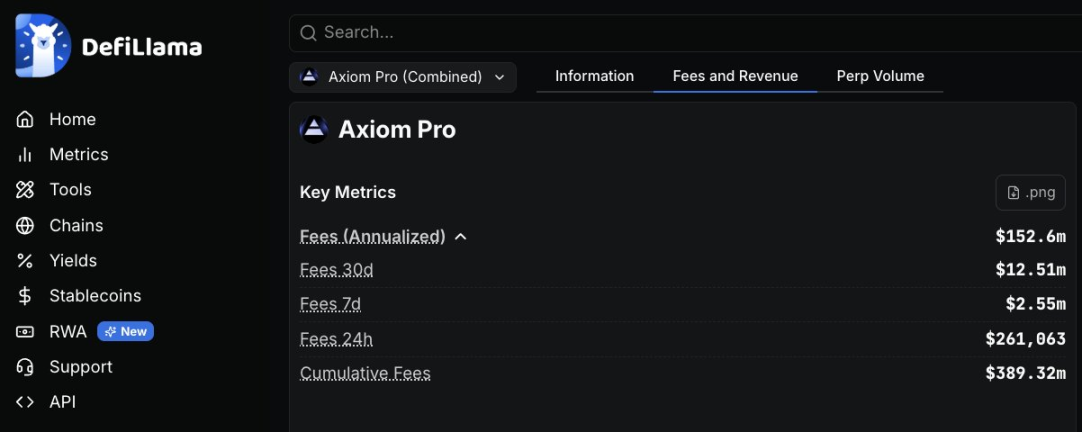
- As a high-revenue platform (cumulative revenue exceeding $390 million), this case may trigger an investigation by the U.S. Attorney's Office for the Southern District of New York (SDNY).
Original Author: ZachXBT
Original Compilation: TechFlow
TechFlow Introduction: On-chain detective ZachXBT has released a full investigative report accusing multiple employees of the crypto trading platform Axiom of abusing internal system permissions for over a year to query users' private wallet information and engage in insider trading. The investigation was commissioned by a client, with evidence including recorded calls, internal screenshots, and on-chain fund flow charts. The implicated employees allegedly planned to help accomplices quickly profit $200,000. Axiom has generated over $390 million in revenue to date. This case exposes significant vulnerabilities in internal permission controls at crypto platforms.
(I)
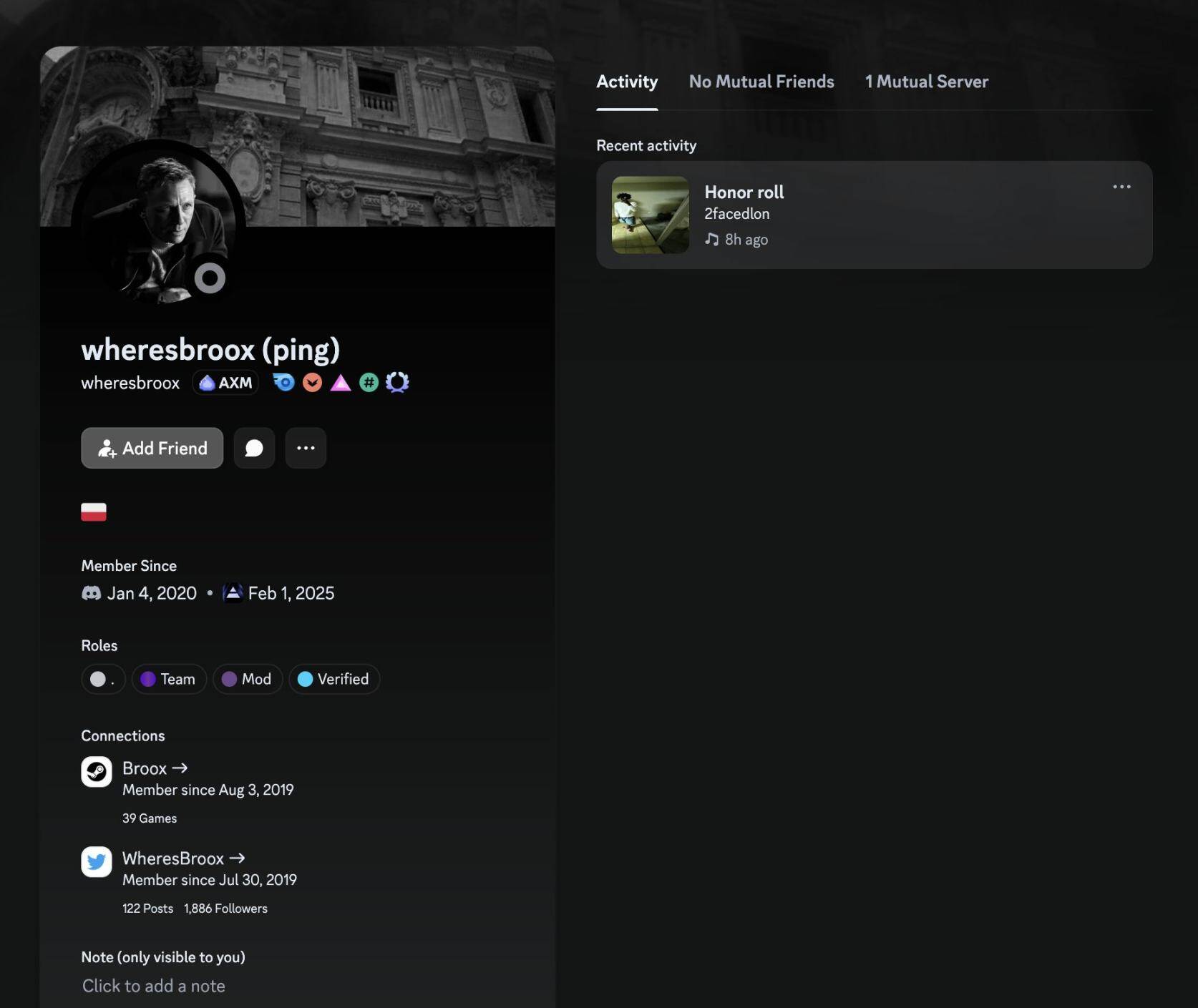
Meet @WheresBroox (Broox Bauer). He is one of several implicated employees at @AxiomExchange, accused of exploiting the lack of permission controls in the company's internal tools since early 2025 to query sensitive user information and conduct insider trading by tracking private wallet activity.
(II)
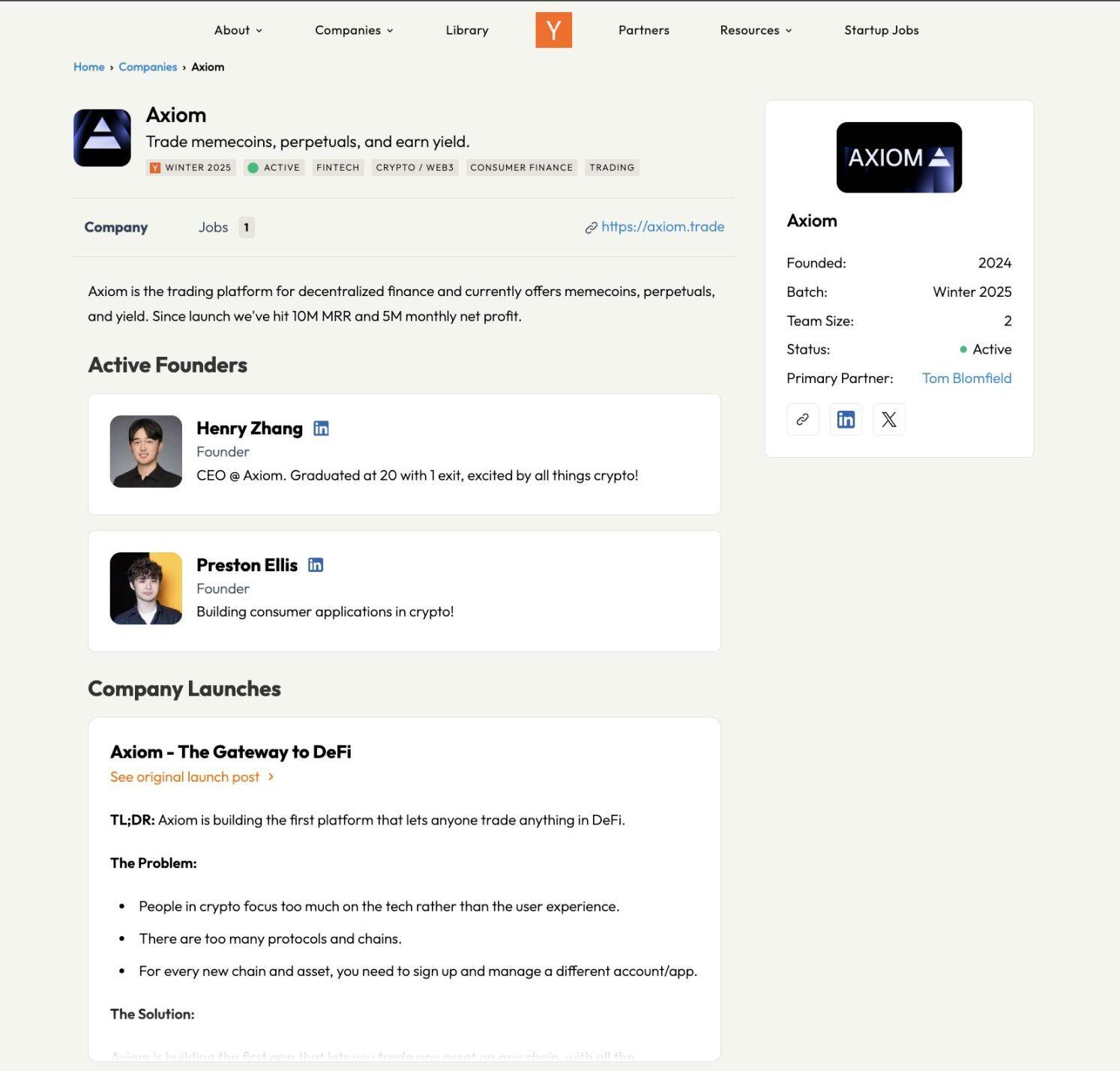
Axiom is a crypto trading platform founded by Mist and Cal in 2024. After incubation in the Y Combinator Winter 2025 batch, it quickly became one of the most profitable companies in the space, with cumulative revenue exceeding $390 million to date.
I was commissioned by a client to investigate allegations of misconduct at Axiom after receiving relevant tips.
(III)
Broox is currently a senior business development employee at Axiom, based in New York.
In a recorded segment, Broox stated he could track any Axiom user via referral codes, wallet addresses, or UIDs, claiming he could "find out everything about this person."
He also described initially checking only 10 to 20 wallets, then gradually increasing over time—"so it doesn't look as suspicious."
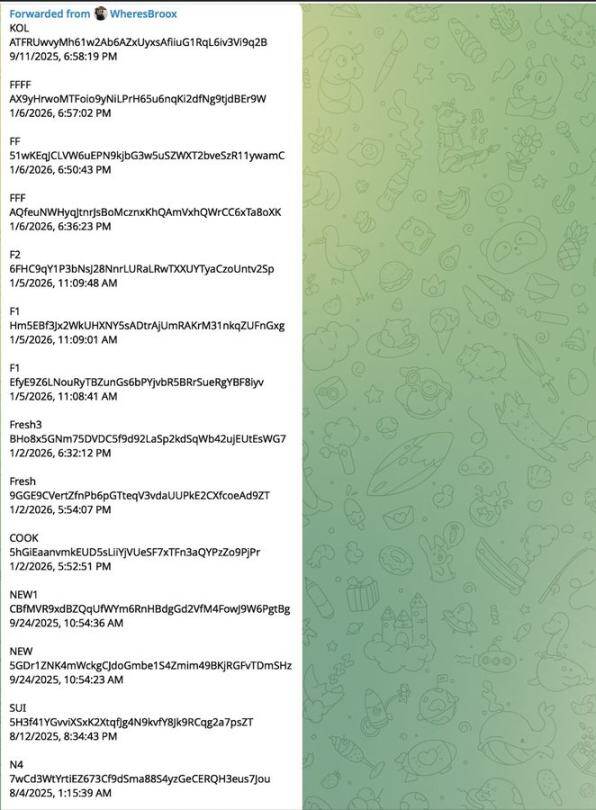
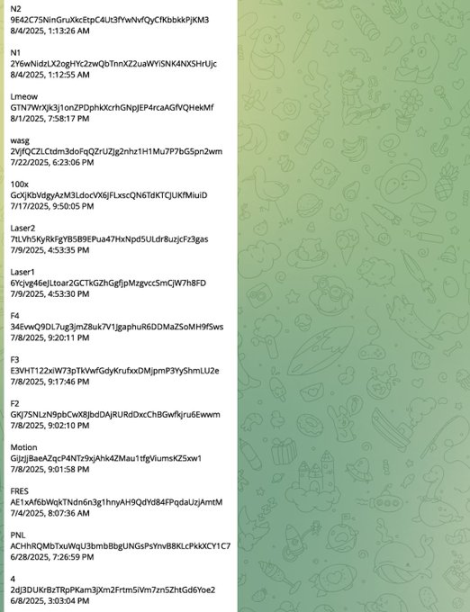
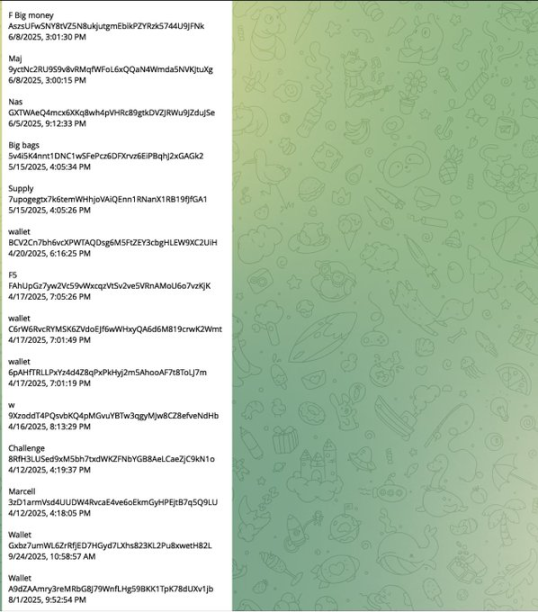
In another segment from the same recording, Broox established rules for team members to request queries from him, saying he would send over the full wallet list.
This full recording comes from a private planning call among members of the group.
(IV)
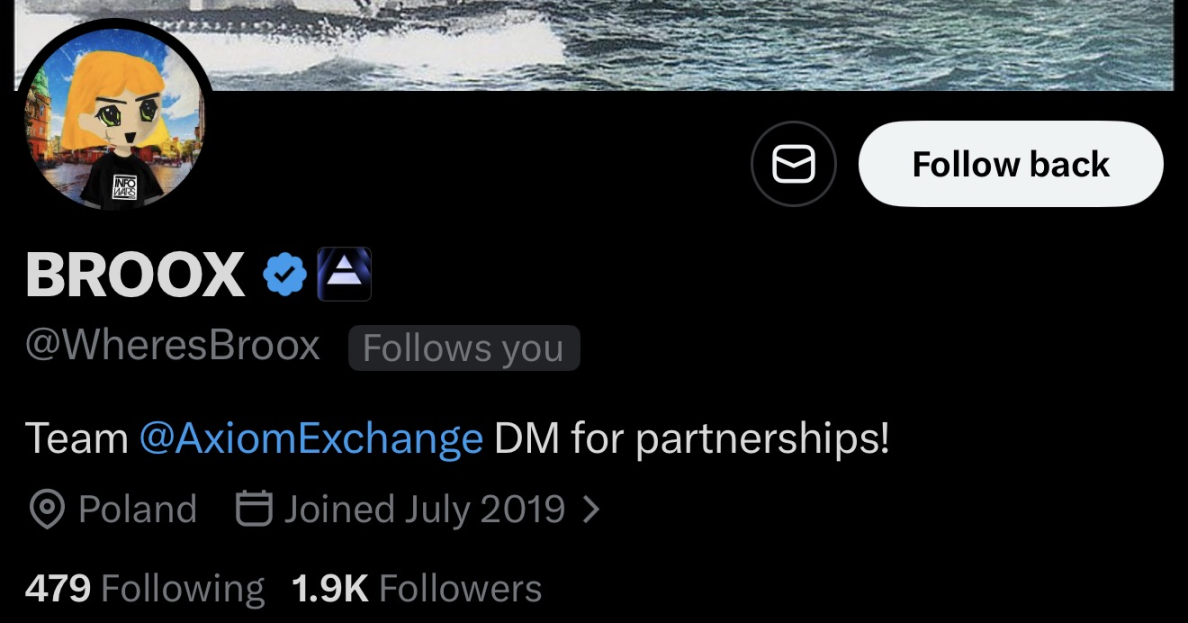
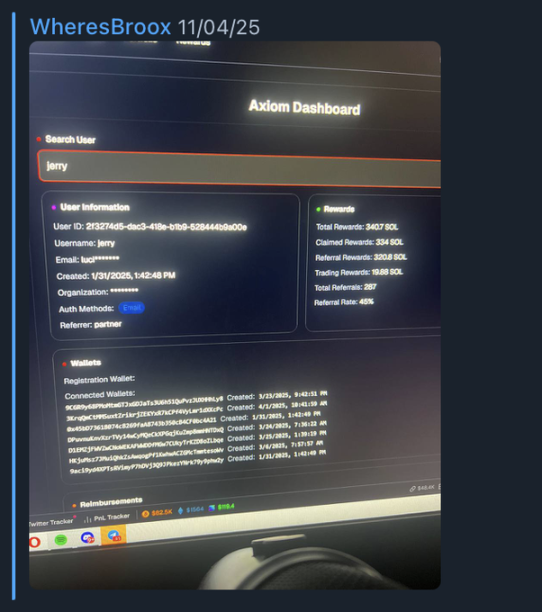
In April 2025, Broox shared a screenshot from Axiom's internal backend showing private wallet information for the trader "Jerry."
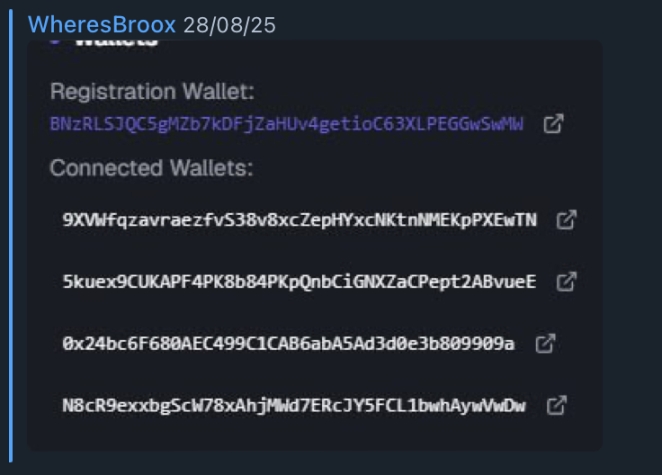
In August 2025, Broox sent a second screenshot showing registration information and associated wallets for the trader "Monix."
Also in August of the same year, Broox discussed querying Axiom users who had traded the meme coin "AURA."
(V)
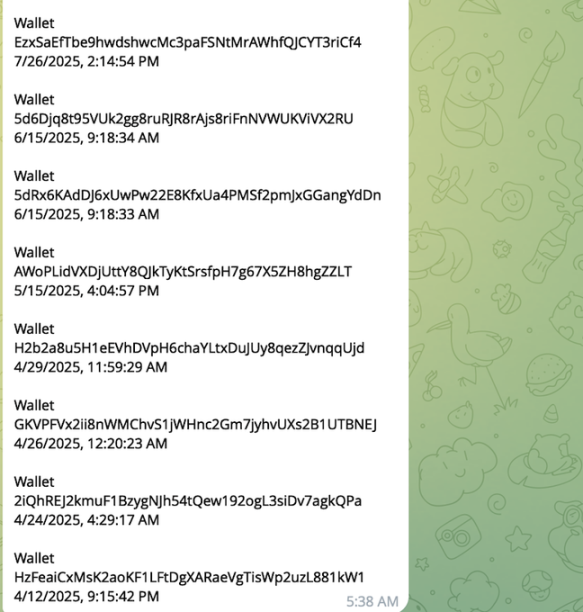
The group created a Google Sheets document compiling wallet addresses for multiple KOL targets. These addresses were compiled from data Broox obtained via Axiom's internal backend.
Several KOLs named in the sheet or appearing in leaked screenshots have been contacted and independently confirmed the accuracy of the wallet data.
(VI)
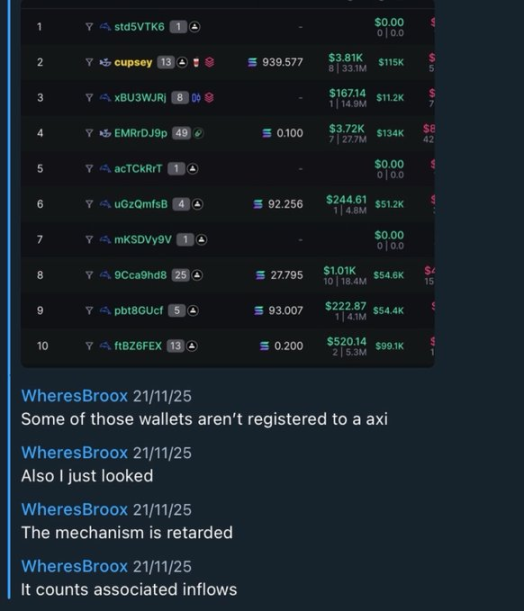
One of the targeted KOLs is Marcell, a trader notorious for using his followers on X and Telegram as "exit liquidity."
He became a target because of his habit of accumulating large amounts of tokens in a private wallet (i.e., "bundled accumulation") before promoting the meme coin to his followers.
Traders like Marcell are ideal targets for this type of abuse—their address reuse rate is low, and their private wallets are almost never public, making privileged internal information extremely valuable.
(VII)
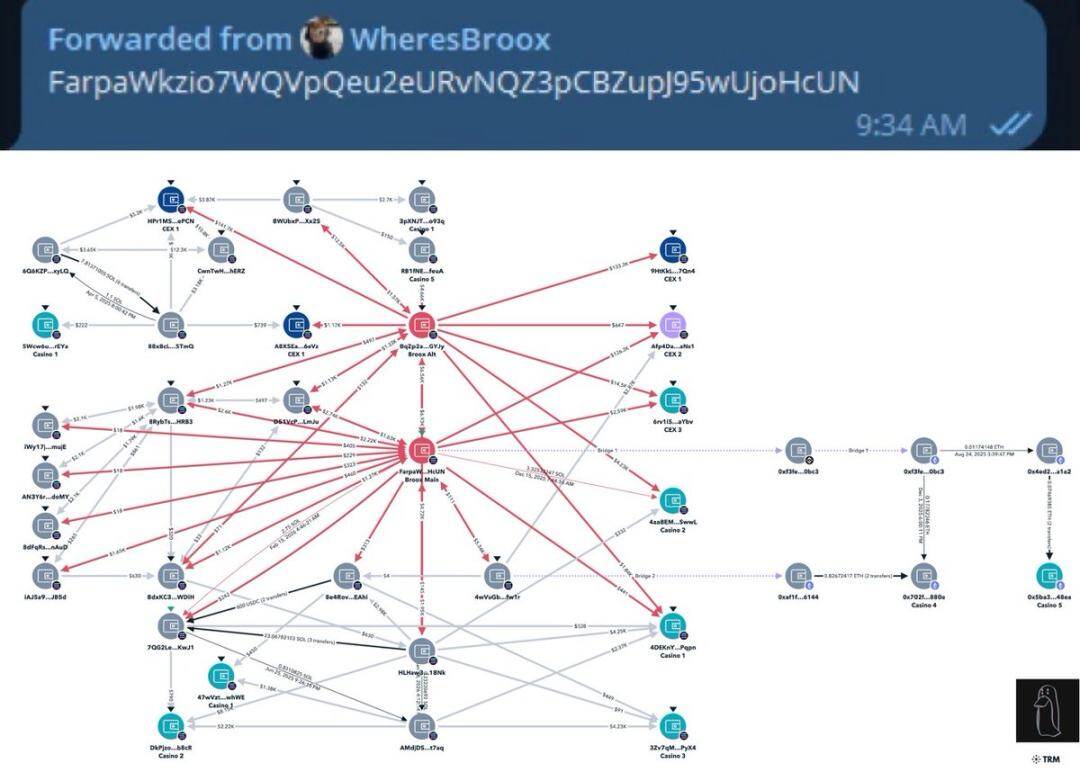
Through private messages, Broox's main wallet was identified, and all directly associated addresses have been mapped.
FarpaWkzio7WQVpQeu2eURvNQZ3pCBZupJ95wUjoHcUN
Due to the associated addresses' heavy involvement in meme coin trading, it's difficult to pinpoint high-confidence insider trading cases based solely on wallet data—unless Axiom's internal logs could be accessed to cross-reference the timing of trade orders.
Funds from the associated addresses primarily flowed to the following centralized exchange deposit addresses:
- 9HtKkLzTVUGMS9BDMSXbVjooP1rVoeiFPj3tEtmj7Qn4
- A8XSEaZXYo8eidAMivoAonf8skBeW1QkfprdBJm6eVz
- HPr1MSrSB2i9r9Vcsj8Cmx2sUFGudpDum6kY9dp2ePCN
- Afp4DargofX8K67BRUuhVuoBy1DJn9vTbH3ico9CaNs1
- 6rv1iSZ7YyR18R7EPvXwHdDkNp3qzrE9YPQtPnLVaYbv
(VIII)
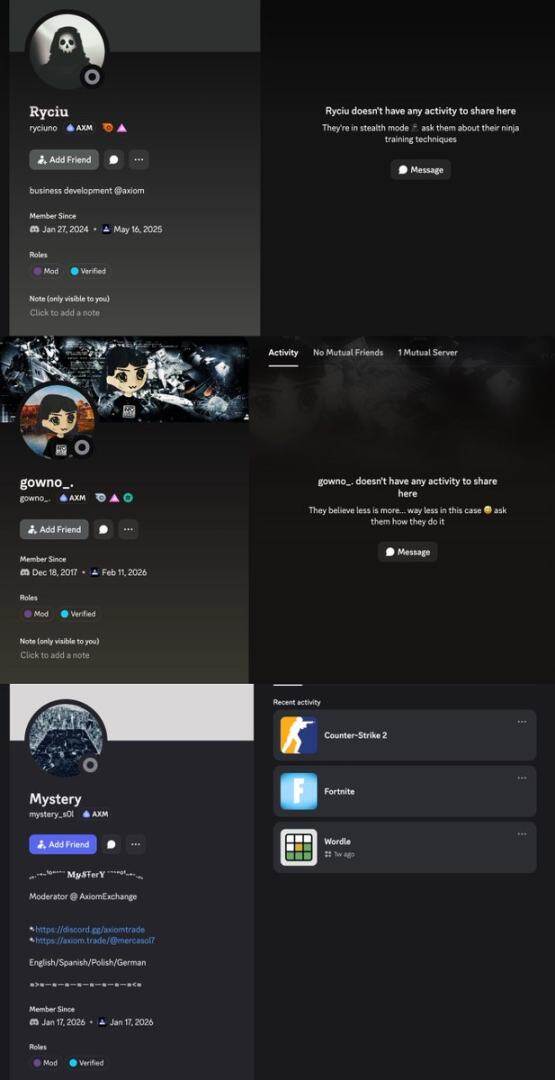
Also on the call with Broox was his friend Gowno (Seb), a moderator who recently joined Axiom.
In the first recording, Broox claimed that Ryan (Ryucio)—another business development employee at Axiom—had used the internal backend to query user information for others and said he helped get his friend Mystery a job as a moderator at Axiom.
In the second recording, Broox discussed how Gowno's responsibilities would expand over time and stated he could eventually assist with wallet queries.
Neither Ryan nor Mystery were present on this recorded call.
(IX)
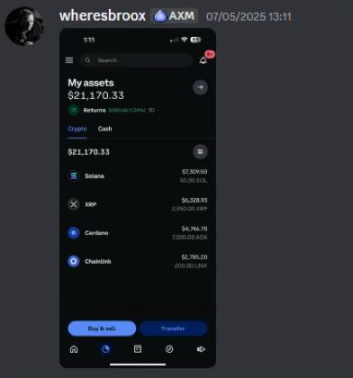
In this recorded call from February 2026, Broox detailed a plan to use his permissions at Axiom to help Gowno quickly profit $200,000. This aligns closely with similar misconduct he has engaged in with others since early 2025.
In private chats, he also shared screenshots of his exchange account balances, indicating this scheme was already generating actual profits.


(X)
This investigation was commissioned by a client. As an independent investigator, I examined the alleged misconduct within Axiom, and the above constitutes the findings.
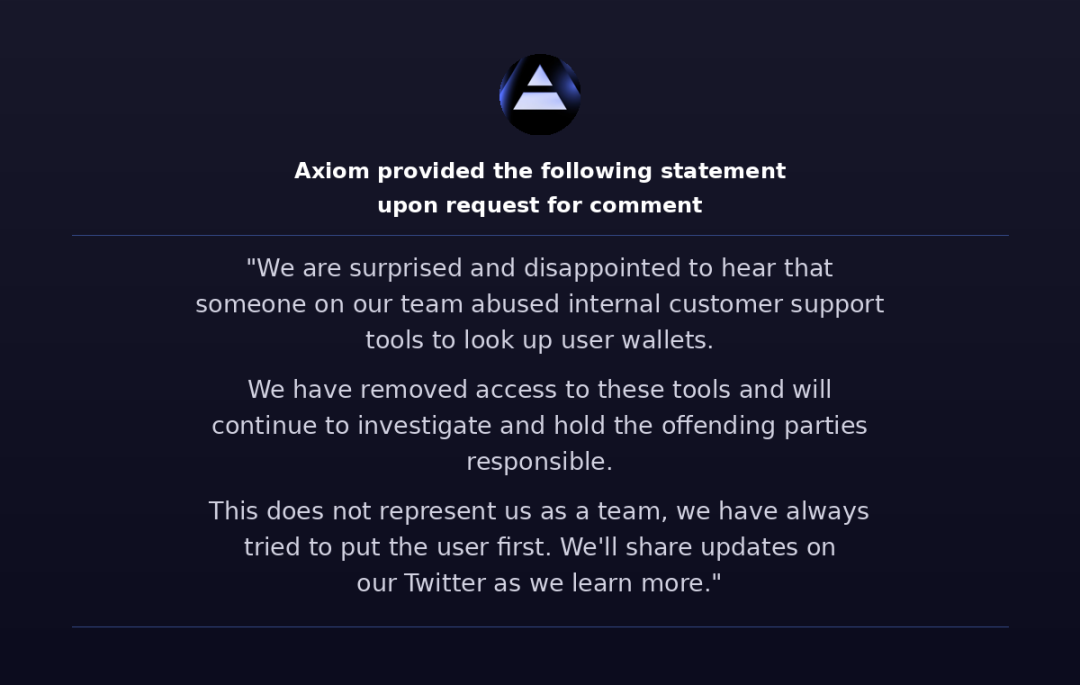
Earlier today, I contacted the Axiom team for comment; their official statement is attached to the original article.
Regardless of whether Cal or Mist were aware, the company had virtually no monitoring mechanisms or access controls in place from the outset to prevent such abuse of power.
The scope of data access granted to employees was quite broad—in an easily accessible backend system, employees could see users' complete wallet lists (including date/time), wallets users were tracking, transaction history, wallet labels, and linked accounts. Such permissions are highly unusual for a business development role.
Given Broox is based in New York, I believe this case could be a good opportunity for the U.S. Attorney's Office for the Southern District of New York (SDNY) to get involved, as it likely falls within their jurisdiction.
Regardless of whether criminal charges are ultimately filed, I hope the Axiom co-founders will conduct a further internal investigation into these abuses and consider legal action against the implicated employees.
Editor's Note: This article is compiled from a tweet-based investigative report; images are screenshots of investigation evidence.



