OKX Web3 & CertiK: MEME "Big Adventure" and Security "Truth"
Introduction: OKX Web3 Wallet has specially planned the "Security Special Issue" column to provide special answers to different types of on-chain security issues. Through the most real cases happening around users, in collaboration with experts or institutions in the security field, dual sharing and answers from different perspectives are conducted, so as to sort out and summarize the rules of safe transactions from the shallow to the deep, aiming to strengthen user security education while helping users learn to protect their private keys and wallet asset security from themselves.
Playing MEME is a big adventure
Rug pull, Pixiu plate, smashing, being clamped...many traps lie ahead
I was a brave risk taker until I took an arrow to the knee
This is the 2nd issue of the Security Special Issue. We have invited CertiK and the OKX Web3 team, two well-known security organizations in the industry, to share common MEME on-chain transaction security risks and prevention measures from the perspective of a practical guide. We hope that this will be helpful to MEME users.

CertiK Security Team: Founded by two professors from Yale University and Columbia University, CertiK uses the most advanced formal verification technology, AI audit technology, and manual audits by security experts to ensure the security of blockchain protocols and smart contracts by scanning and monitoring them. To date, CertiK has been recognized by more than 4,000 corporate customers, has discovered nearly 70,000 code vulnerabilities, and has protected more than $400 billion in digital assets from loss.
OKX Web3 Wallet Security Team: Hello everyone, I am very happy to share this. The OKX Web3 Wallet Security Team is mainly responsible for the security capability building of the OKX Web3 Wallet, providing multiple protection services such as product security, user security, and transaction security. While protecting the security of user wallets 24/7, it also contributes to maintaining the security ecosystem of the entire blockchain.
Q1: Real cases of MEME risks happening around you
OKX Web3 Wallet Security Team: There are many types of risk cases of this type. We have selected several classic cases that users encountered when trading MEME:
Case 1: Pixiu Plate
User A saw a hot MEME discussion on Twitter and found the token address in the comments of the MEME tweet. After checking the transaction data of the MEME, he found that it performed well, so he bought it. As the price of the MEME continued to rise, User A wanted to sell it and lock in profits, but he was unable to sell it. After investigation by our team, we found that the MEME token was a Pixiu disk, and the user's address could not be sold because it was blacklisted.
Case 2: Malicious Rug Pull
User B often speaks and participates in activities in a Telegram community, and is added as a contact by many group members. One day, a group member privately chatted with user B and recommended a MEME project to him, saying that the project was very popular and had great potential, and then immediately provided the address of the MEME token. User B was a little tempted, so he checked on a data analysis tool and found that the liquidity LP of the MEME token had been destroyed and there were no whales holding positions. Therefore, he believed that the MEME project was more reliable and purchased it. However, on the second day, user B suddenly discovered that the liquidity of the MEME project had been exhausted. After investigation by our team, it was found that the token was a malicious Rug Pull token, which had a backdoor logic that could issue a large number of tokens.
There are endless risk cases happening to MEME users. We hope that through the following conversations, we can provide users with some safety reference guides. This does not constitute any investment advice and is only for learning and communication.
Q2: Common risks on the EVM public chain and Solana network when trading MEME
CertiK Security Team: MEME risks are divided into two categories: one is the on-chain risk scenario, and the other is general risk, which has nothing to do with blockchain technology.
Before introducing specific on-chain risk scenarios, let us first introduce the general risks, which mainly include five categories: extremely low coin issuance costs, easy manipulation of token prices, highly centralized projects, large investor transaction wear and tear, and Rugpull scams.
1. The cost of issuing coins is extremely low
Generally speaking, the amount of technical development for launching MEME projects is extremely low or even non-existent, which has led to the emergence of one-click token issuance tools such as PandaTool. It is precisely because of the extremely low development cost that the cost for internal project personnel and early investors to obtain tokens is extremely low. In addition, the MEME project itself has no actual fundamentals. Once the market is no longer "FOMO" (Fear of Missing Out), these extremely low-cost tokens will be quickly sold, causing subsequent investors to bear huge losses.
2. Token prices are easily manipulated
The price of MEME is easily manipulated, partly because of its lack of substantial technical support, intrinsic value, and low issuance threshold, which makes it easy for anyone to create and issue MEME, making the market flooded with a large number of highly speculative currencies.
At the same time, MEME usually relies on social media and network popularity to drive its price, and these factors are extremely vulnerable to manipulation by large or organized groups. These speculators can manipulate prices by buying or selling in large quantities, as well as creating false information and market noise, causing drastic price fluctuations and attracting more retail investors to chase ups and downs, thereby further exacerbating the possibility of price manipulation.
3. The project is highly centralized
MEME projects usually lack a decentralized governance mechanism, and decision-making power is concentrated in the hands of a few developers and core teams, making project direction and management susceptible to personal interests, increasing investor risks. Based on the centralization of decision-making power, there may also be various centralized risks such as the centralization of control over token contracts and programs, the centralization of token holdings, and the centralization of liquidity control.
4. Investors experience significant trading wear and tear
MEME transactions are prone to high friction, primarily due to its poor liquidity. Since there are relatively few participants in the market who buy and sell MEME and the trading volume is insufficient, this leads to a large bid-ask spread (i.e., the gap between the buying price and the selling price), which increases transaction costs. In addition, MEME coins with poor liquidity are prone to drastic price fluctuations in large transactions, further increasing transaction risks and costs. Investors often need to endure higher slippage and greater price impact when buying or selling, resulting in inefficient transactions and increased transaction costs.
The second is attributed to the "transaction tax" mechanism. In order to incentivize investors to hold or maintain project funds, many MEME projects usually charge a certain percentage of transaction taxes on each transaction. These taxes are usually used to repurchase tokens, reward holders, or support project development. However, this transaction tax increases transaction costs, making frequent transactions more expensive. Traders need to pay additional taxes every time they buy or sell, which increases transaction wear and tear and further reduces liquidity. Investors must bear higher fees and risks when conducting MEME transactions.
5. Rugpull scam
MEME is easily targeted by Rugpull scams due to its high anonymity, lack of transparency and regulation. The following are several common Rugpull methods and their phenomena:
1) Liquidity Pull:
Method: The development team will create a liquidity pool on a decentralized exchange (DEX) and add tokens and mainstream cryptocurrencies (such as ETH, USDT, etc.) to the pool. After attracting enough investors, the development team will suddenly withdraw all liquidity, making the tokens untradable.
Phenomenon: Investors found that they could not sell tokens, the token price quickly returned to zero, and the liquidity pool showed that there was almost no funds left.
2) Developer Dumping
Method: Project owners or early holders hold a large number of tokens. When market demand is driven up, they will sell most or all of their tokens in a short period of time, causing prices to plummet.
Phenomenon: Huge sell orders appear in the transaction records, token prices fall sharply, market confidence collapses, and trading volume decreases rapidly.
3) Fake Projects:
Method: Criminals will create a fake MEME coin project, fabricate a false vision and roadmap, and attract investors through social media and celebrity endorsements. Once enough funds are raised, they will shut down the project and run away with the money.
Phenomenon: Project websites and social media accounts suddenly disappear, the development team cannot be contacted, and the value of tokens in investors' accounts depreciates rapidly.
4) Contract Exploits:
Method: The development team intentionally leaves backdoors or vulnerabilities in the smart contract, allowing them to manipulate the contract under certain conditions and steal investors' funds.
Phenomenon: Token transactions are abnormal or suddenly stopped, investors are unable to transfer or sell tokens, and the contract address shows that a large amount of funds have been transferred to an unknown account.
5) Fake Forks:
Method: Claiming to upgrade or fork the original tokens and requiring holders to exchange old tokens for new tokens, in fact, is to collect and possess these old tokens.
Phenomenon: Old tokens lose value, so-called new tokens cannot be traded on any exchange, and the project team loses contact.
Next, we will introduce the common on-chain risks when users conduct MEME transactions on the EVM public chain & Solana network. In order to facilitate users to more directly compare the differences in risk types, we share them in the form of a table.

Image credit: CertiK Security Team
OKX Web3 Wallet Security Team: EVM public chains and Solana are the preferred networks for users to conduct MEME transactions. There are differences in the types of on-chain risks between the two, which is related to factors such as their different token issuance mechanisms.
First, EVM-based public chains. Since EVM-based public chains have a high degree of freedom in issuing tokens and the token content is implemented by developers, there are currently two types of common on-chain risks for MEME transactions on EVM-based public chains:
1. MEME with malicious logic
When MEME is hot in the market, various malicious tokens that are forged to look like popular MEME will appear. These malicious tokens usually have good transaction data, which will lead users to misjudge and trade malicious tokens, thus causing losses. There are currently two main types of common malicious tokens:
1. Pixiu disk: refers to tokens that can only be bought but not sold. This type of malicious token usually sets a 100% tax rate or special transfer restriction logic, making it impossible for users to sell tokens.
2. Malicious rug pull tokens: refers to tokens with hidden issuance logic. This type of malicious token exhausts token liquidity by hiding the issuance logic and then issuing additional tokens.
(II) Project owners committing evil acts
Currently, there are two main types of malicious behavior by project parties: malicious behavior using privileged functions and direct market crashes.
1) Privileged functions: Project owners use privileged functions, such as the mint function, to issue additional tokens to crash the market.
2) Direct dumping: The project owner directly uses the tokens they hold to dump the market.
Second, the Solana chain. It is worth noting that the Solana network issues tokens through fixed official channels. Therefore, when conducting MEME transactions on the Solana chain, the common on-chain risks mainly come from the project party's malicious behavior.
1. Privileged functions do evil
The project owner uses privileged functions, such as the mint function, to issue additional tokens to dump the market; or uses freeze instructions to freeze user addresses, thereby achieving a purpose similar to the Pixiu plate, preventing users from selling.
(II) Directly crashing the market
The project owner directly uses the tokens held to dump the market. It is worth noting that some malicious MEME project owners will evade the review of concentrated token holdings by distributing the tokens held.
Q3: Which dimensions or tools can be used to initially filter out MEME projects with extremely high risks?
CertiK Security Team: This does not constitute any investment advice. It is just an introduction to some tools that we personally use. It cannot help users filter risks 100%. It only provides a reference for users to initially judge whether a MEME has a high risk.
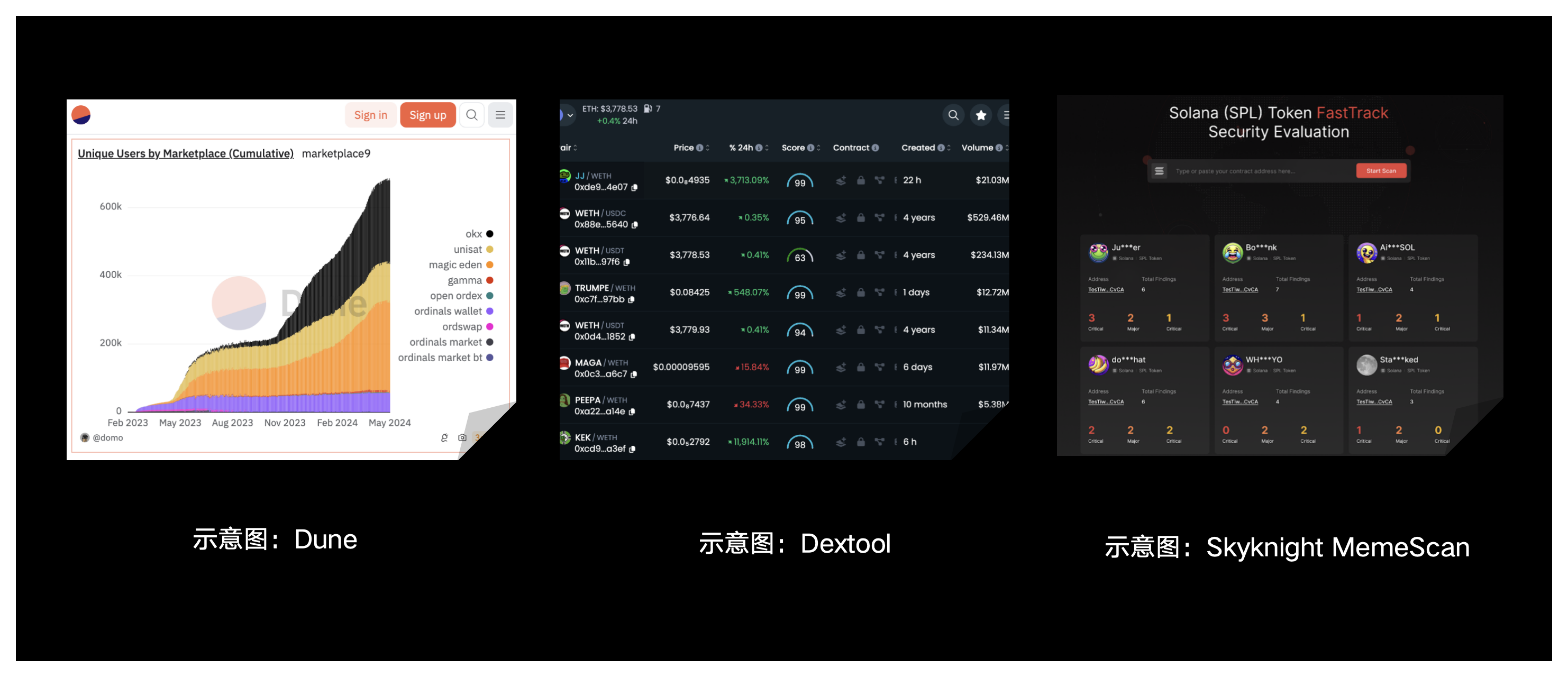
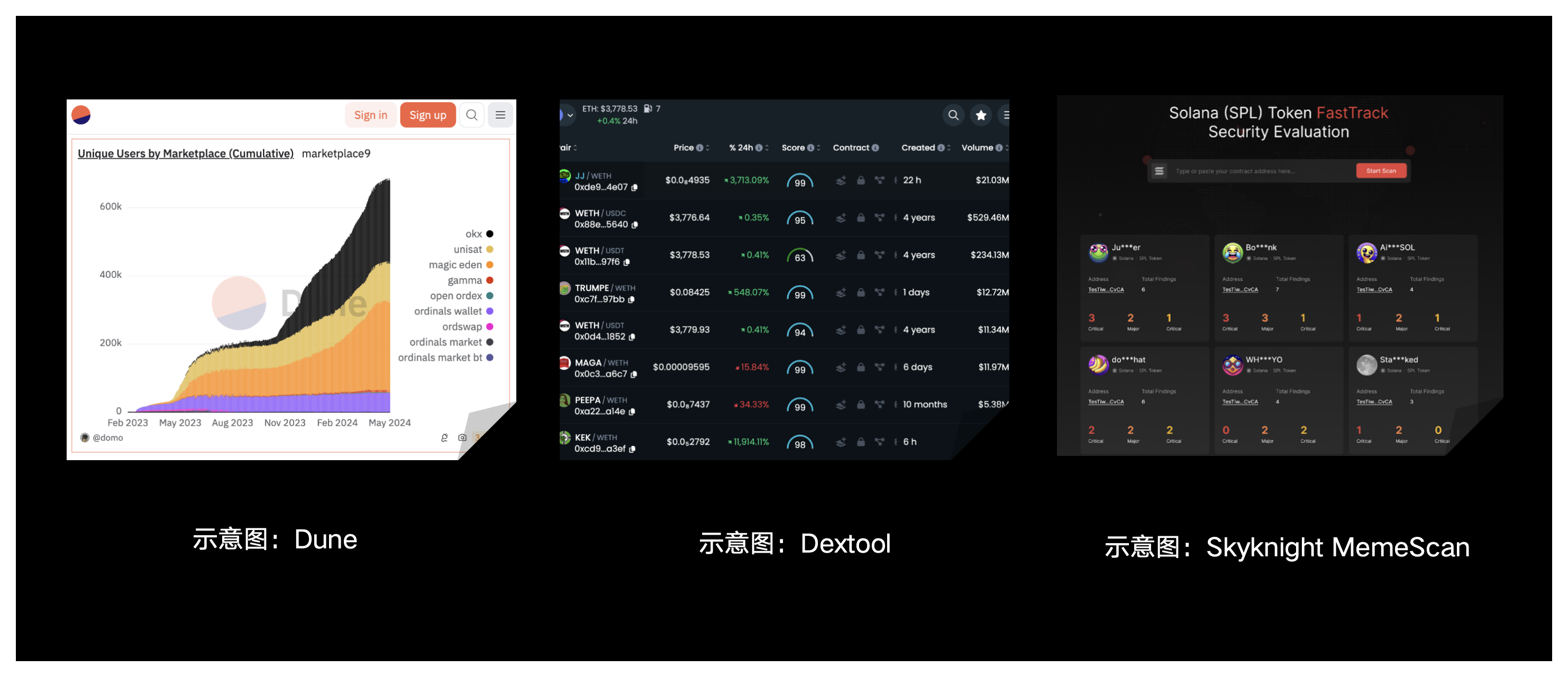
1) dune.com: A data analysis platform that allows you to customize queries to analyze and monitor on-chain data of tokens. It is relatively flexible, but relatively complex to use and requires a certain amount of learning cost.
2) Dextools.io: A token information integration platform that can view some basic information of tokens, such as market value, liquidity, number of holders, token distribution, etc., and can also perform some simple security risk screening.
3) Skyknight MemeScan: A new platform launched by CertiK that provides a solution for evaluating the security status of MEME. The platform provides instant insights and on-chain behavior analysis, including contract minting analysis, transaction control detection, ownership concentration analysis, liquidity control assessment, and more.
OKX Web3 Wallet Security Team: There is no way or method to filter out risks 100%, but from the perspective of token security and project health, we provide users with several dimensions that can initially filter out highly risky MEME items. It should be noted that users cannot judge the security of a project based solely on the following dimensions.
1) Smart contract security: Auxiliary tools can be used to verify whether there are security issues at the source code level. These tools can check whether there is malicious logic in the project code and identify security vulnerabilities in the code itself. In addition, the permission control of the contract needs to be evaluated to ensure that the contract owner does not have too much authority to avoid the ability to issue or destroy tokens at will.
2) Token distribution and holding distribution: Check the distribution of token holders through the blockchain browser and avoid participating in projects with too concentrated token holdings, as these projects are easily manipulated and have a higher risk of rugpull.
3) Liquidity and trading activity: Observe the trading volume and price fluctuations of the token. Low trading volume and high volatility may mean that the project is unstable or there is a risk of manipulation.
4) Community and development team activities: Whether the project team is open and transparent, including the background, experience, and social media activities of team members.
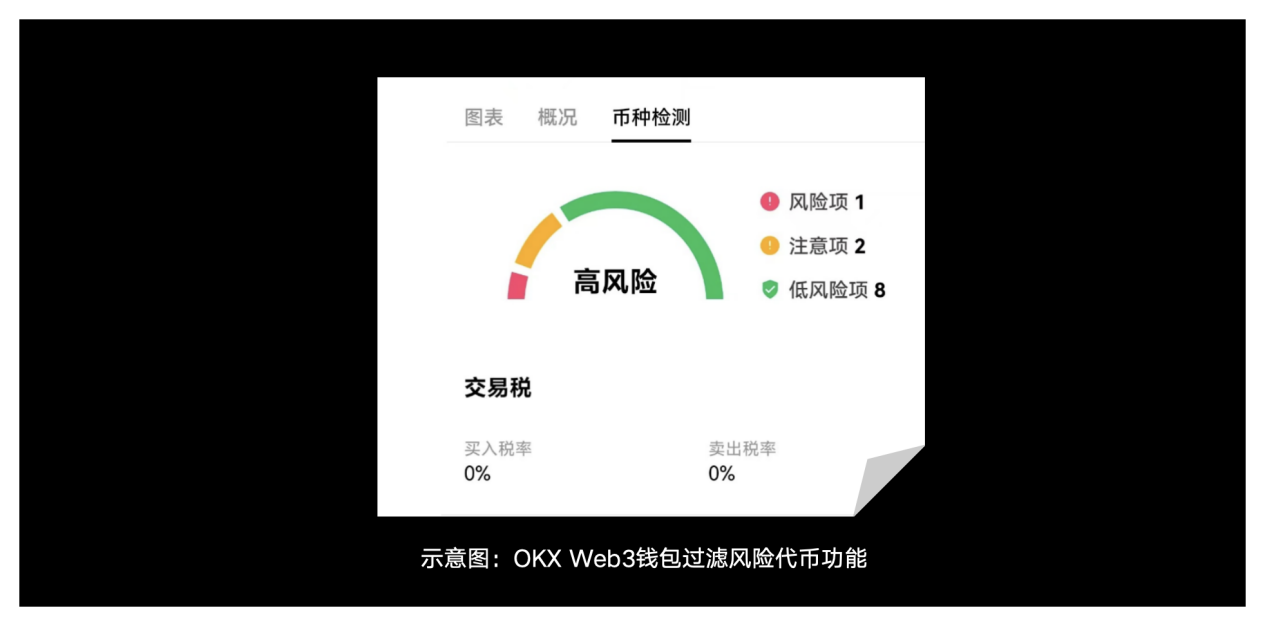
Currently, the OKX Web3 wallet also provides users with the ability to filter risky tokens, filtering out tokens that may cause damage to users from multiple levels such as code security and transaction security. While providing token information in various dimensions, it also protects users' MEME safe transaction experience.
Q4: As an early circulation place for MEME tokens, what limitations or risks do Launchpad platform and DEX currently have?
CertiK Security Team: First of all, Launchpad platforms and DEXs must have strong technical support to cope with the transaction response speed and transaction scale of the MEME project. In addition, liquidity is also a crucial link, and relevant platforms need to monitor any events that may affect liquidity security. Finally, regarding the compliance risks of MEME, the platform must understand and implement relevant regulatory policies and requirements to reduce possible legal risks.
OKX Web3 Wallet Security Team: Next, we will introduce the current limitations or risks of the Launchpad platform and DEX respectively.
For the Launchpad platform, there are three main points:
First, the quality of projects launched on the platform varies. Although some Launchpad platforms conduct reviews and due diligence, they may still fail to fully identify high-risk or low-quality projects.
Second, fund management risk. Launchpad platforms usually centrally manage a large amount of user funds. If these funds are not properly managed or misappropriated maliciously, they may lead to user fund losses. In addition, the platform may lack sufficient safeguards to protect the safety of user funds.
Third, market manipulation: Project owners or large capital players may manipulate prices after the launch of Launchpad, causing drastic market fluctuations and affecting retail investors.
For DEX, there are relatively more limitations
First, there is insufficient liquidity. Newly listed MEME usually has poor liquidity on DEX, which can easily lead to large transaction slippage and drastic price fluctuations.
Second, smart contract vulnerabilities. DEX relies on smart contracts for transactions. If these contracts have vulnerabilities, they may be exploited by hackers and cause financial losses.
Third, transaction fees are high, especially on networks such as Ethereum, where transaction fees (gas fees) can be very high, affecting the cost-effectiveness of small traders.
Fourth, malicious project parties, anyone can deploy tokens and launch DEX transactions. Some project parties may deliberately leave backdoor functions in the contract, allowing the project parties to arbitrarily manipulate the token balance or prevent users from selling tokens.
Fifth, the user experience issue. The operation of DEX is relatively complicated for ordinary users, involving wallet connection, gas fee setting, etc. For entry-level users, the experience may not be as good as that of centralized exchanges (CEX).
Q 5: Let me ask you a follow-up question. Telegram robots represent one of the practical manifestations of intent-based interactions in the field of cryptocurrency. Does this represent the future development trend of DEX?
CertiK Security Team: Telegram bots can significantly lower the barrier to entry and automate some of the steps in a transaction, making it more convenient for non-professionals to trade cryptocurrencies. However, special attention must be paid to the specific security risks of these bots. It is recommended to conduct a comprehensive security due diligence on any third-party dApp that interacts with the wallet to ensure its security.
OKX Web3 Wallet Security Team: The application of Telegram robots in the field of cryptocurrency has demonstrated great potential for intent-based interaction. This trend is expected to promote the future development of decentralized exchanges (DEX) by optimizing user experience, enhancing transaction convenience and security, expanding the financial services ecosystem, and technological innovation.
1. Improve user experience
Simplify operations: Telegram robots use natural language processing to enable users to conduct transactions using simple chat commands, simplifying complex operation processes.
Automatic trading: Users can set automatic trading rules, such as stop loss and take profit points, to reduce the risk and time cost of manual operations.
2. Enhance decentralized transactions
Seamless integration: The robot is integrated with the decentralized exchange (DEX) through an API interface, hiding complex trading operations and reducing users’ learning costs.
Real-time operation: The robot can monitor market dynamics in real time and notify users instantly, enabling them to make trading decisions and execute transactions quickly.
3. Improve safety
Smart Contracts: Robots use smart contracts to ensure transparency and security of transactions, reducing the possibility of human intervention and fraud.
Decentralization: Although the bot may be centralized, the actual transactions take place in a decentralized environment, increasing the security and transparency of transactions.
4. Expanding the Ecosystem
Multi-functional platform: Telegram robots are not limited to transactions, but can also be extended to financial services such as asset management, lending, staking, etc., providing a one-stop financial solution.
Enhance community interaction: Through the Telegram platform, robots can promote user communication and community building, and increase user engagement.
5. Technology and market drivers
Innovation-driven: Advances in artificial intelligence and blockchain technology will make robotic applications increasingly intelligent and efficient, and promote the emergence of more decentralized applications and services.
Market acceptance: Users’ growing demand for simplified and automated services is driving more DEXs to adopt robotic services to improve their competitiveness.
Q 6: What are the current safety risks of high-frequency tools, such as various TG BOT robots?
CertiK Security Team: As the cryptocurrency market develops, Telegram BOT robots are becoming more and more common in transactions and information acquisition. However, these frequently used tools also bring significant security risks. Users should pay special attention to the following aspects when using them.
First, many Telegram BOT robots have not been audited or their codes have not been made public, and they may contain malicious code or vulnerabilities. These malicious BOTs may steal users' private keys, identity information, or other sensitive data. In addition, malicious BOTs may disguise themselves as legitimate services and use phishing attacks to trick users into entering their private keys or mnemonics to steal funds. Therefore, users should make sure to only use officially recommended or verified BOTs and avoid clicking on unknown links or entering sensitive information.
Secondly, some BOTs may request too many permissions, such as access to the user's contacts, files, or other private information. When using, permissions should be granted with caution to ensure that the BOT only obtains the minimum permissions required for its normal operation. At the same time, the communication between the BOT and the Telegram server may be intercepted by a man-in-the-middle attack, resulting in data leakage or tampering. Users should ensure that they use BOTs with encrypted communication and check the implementation of their secure communication protocols.
Third, many Telegram BOTs offer automated trading functions, but if there are loopholes in the trading logic of these BOTs, it may lead to serious financial losses. Users should conduct sufficient testing before using such functions and monitor trading behavior to prevent abnormal situations. In addition, BOT developers may collect and store a large amount of user data. Once this data is leaked or abused, user privacy will be seriously threatened. Users should choose BOTs with good reputation and privacy policies, and regularly check their privacy protection measures.
Finally, over-reliance on certain BOTs for trading or managing assets may result in users being unable to operate normally when the BOT service is interrupted or shut down. Therefore, users should avoid over-reliance on a single BOT and prepare backup plans. By understanding and preventing these risks, users can use Telegram BOT robots more safely and protect their assets and privacy.
OKX Web3 Wallet Security Team: BOT robots like TG provide convenient services but also bring great risks. Next, we will give an example.
First, the centralized custody risk of private keys. Most Telegram robots need to host the user's private key in order to actively sign and send transactions. This means that the user's private key is stored on a third-party server, increasing the risk of theft or abuse.
Second, there is the risk of phishing. Phishing links sent through Telegram robots may trick users into clicking on them, leading to the theft of account information or private keys. In addition, artificial induction in the chat window (such as fake customer service) may trick users into giving away their mnemonics or other sensitive information.
Third, Trojan risk. Some robots may infect users’ devices by sending malware (Trojans) or malicious SDKs, thus endangering the security of the entire system.
In short, users need to be cautious when using various BOT robots, do not click on unfamiliar links at will, and do not disclose their private keys.
Q 7: Misunderstandings and risk prevention when users trade MEME
CertiK Security Team: First, users should conduct security due diligence on any dApp that interacts with their wallet, including exchanges and Telegram bots. Choosing dApps that have undergone security audits can reduce the risk of being attacked during operation and ensure the security of their private keys and identity information. Currently, CertiK helps users reduce risks by providing dApp penetration testing services.
Secondly, MEME transactions are highly dependent on the response speed and frequency of transactions, so it is crucial to choose a stable platform with reasonable transaction fees. When trading, try to choose platforms that are safe, stable, fast, and have low transaction fees to get a better trading experience. For example, the MemeScan platform launched by CertiK mentioned above can provide instant security status information, including on-chain behavior analysis of MEME. For example, contracts can issue new coins, transactions can be suspended or restricted, a few addresses control most of the tokens, a few addresses control most of the liquidity, etc., hoping to provide some help for users to trade safely.
OKX Web3 Wallet Security Team: Considering security, users need to be aware of safe operations and risk prevention when conducting MEME transactions to ensure the correctness and security of transactions.
First, choose the right trading platform. Users should choose a reputable and highly secure cryptocurrency exchange and try to avoid using unverified or unknown trading platforms, which may expose them to the risk of asset theft. For on-chain transactions, confirm the project's official website and the correctness of the contract.
Second, enable a more secure authentication method. For greater security, users can enable two-factor authentication on all trading platforms and wallets, using Google Authenticator or other security applications. Try to avoid SMS authentication, as it is vulnerable to SIM card swap attacks.
Third, use a highly secure wallet. Users should try to use verified wallets for transactions and ensure that the mnemonics or private keys are securely backed up and stored in a safe place to avoid electronic backups. Without backing up the private keys or mnemonics, assets will not be recoverable when the device is lost or damaged.
Fourth, guard against phishing. Users need to always verify the URL used for transactions to ensure that it is an official link. When encountering problems, make sure to contact the official customer service, ignore private messages in Telegram, Discord and other groups, never click on unknown links, sign signatures whose contents you do not know, and display private keys.
Fifth, a secure network environment. Users should operate under a trusted operating system and try not to use public wireless networks.
Finally, thank you for reading the 02nd issue of the OKX Web3 Wallet "Security Special Issue". We are currently preparing the 03rd issue, which will include real cases, risk identification, and security operation tips. Stay tuned!
Disclaimer
This article is for reference only and is not intended to provide (i) investment advice or investment recommendations; (ii) an offer or solicitation to buy, sell or hold digital assets; or (iii) financial, accounting, legal or tax advice. Holding digital assets (including stablecoins and NFTs) involves high risks and may fluctuate significantly or even become worthless. You should carefully consider whether trading or holding digital assets is suitable for you based on your financial situation. Please be responsible for understanding and complying with local applicable laws and regulations.



